Microsoft’s Windows Defender AV Earns “Top Product” Award in June 2019 Antivirus Comparison
Microsoft’s Windows Defender AV just received the top score and “Top Product” award from the independent German institute, AV-Test. Wow, that’s not something you hear very often! In fact, one of the most common statements that we hear when discussing cloud security with Microsoft 365 is: “Microsoft made the security abomination that is Windows XP, allowed exploit kits like EternalBlue to be developed, and every ransomware attack we hear about in the news targets Windows. If Microsoft knows how to write secure code, why don’t they start with Windows?”
Even as a Microsoft Gold partner, we used to agree with comments like that. From deploying Intune using the old Silverlight portal (Intune was rewritten in .NET in 2017 and broken into 50+ microservices in 2018) and using the initial release of conditional access, Microsoft’s security portfolio used to be a giant dumpster fire sitting on top of shards of broken glass from a vulnerability ridden Windows OS.
However, through several acquisitions in recent years and an org-wide restructuring, Microsoft has been asserting its clout as a top cybersecurity vendor that now offers over 90+ security products. With Windows 10 centerstage, it sports some of the most advanced security technologies currently available.
Windows Defender AV Consistently tops Antivirus Comparison Charts
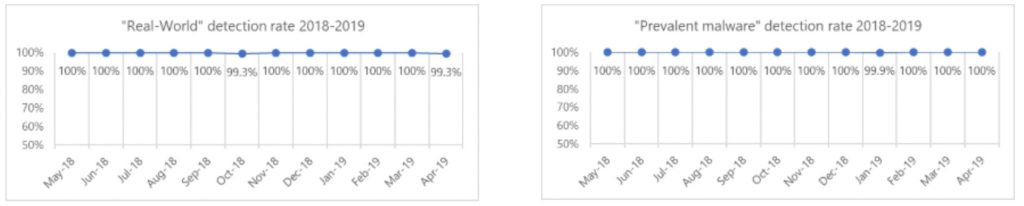
AV-TEST, an independent cybersecurity firm, spent two months continuously testing 20 home-user security products, and the results were striking. Only four of the 20 products achieved a flawless score. Of those four, only one product is available without a paid subscription. As you can guess, the top-performing free service took the “Top Product” award. (Yes, it’s Windows Defender.) Microsoft can now add this distinction to its consistent nearly-perfect detection rates.
Want to know more about how the av comparison results are generated? Check out this transparency report for the May 2019 antivirus test results.
Microsoft’s Journey to Becoming a Cybersecurity Titan
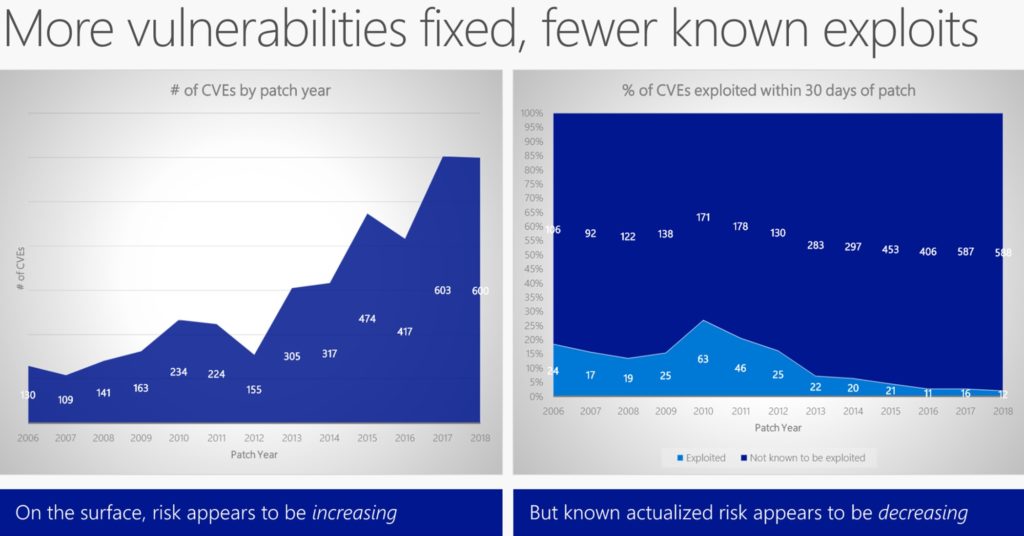
When Satya Nadella took over as CEO for Microsoft in 2014, most exploits were the result of Microsoft not issuing security patches fast enough. Fast forward to 2019 and Microsoft is really on top of issuing patches within 30 days of discovering a common vulnerability exposure (CVE).
Combine the internal efforts to secure the Windows codebase, as seen in the charts above, with the following acquisitions, and you can see how Microsoft has propelled itself into a front-runner in cloud cybersecurity.
- PhoneFactor (2012) creates MFA Server and later Azure MFA for multifactor authentication
- InMage (2014) creates Azure Site Recovery for business continuity planning
- Aorato (2014) creates Advanced Threat Analytics, and later Azure ATP for user behavioral monitoring
- Adallom (2015) creates Microsoft Cloud App Security for shadow IT discovery and anomalous activity reports
- Hexadite (2017) improves automatic incident investigation in Microsoft Defender ATP (formerly Windows Defender ATP)
- GitHub (2018) turns into Azure DevOps (which also hosts our DevSecOps platform Secqur Æther)
- Windows Defender ATP rebrands to Microsoft Defender ATP after adding support for MacOS in early 2019
- BlueTalon (2019) to improve Data Privacy and Governance management
So when discussing ransomware in the news, a more complete statement would be: every major ransomware attack we hear about targets Windows…and it likely could have been prevented if the organization was simply enforcing patch deployments within 30 days of release and updating Windows Defender AV signatures daily. And don’t forget:
Windows Defender AV comes with every version of Windows 10. At no extra cost! No need to try understanding Microsoft 365 licensing SKUs.
Next-Generation Antivirus with Microsoft Defender ATP
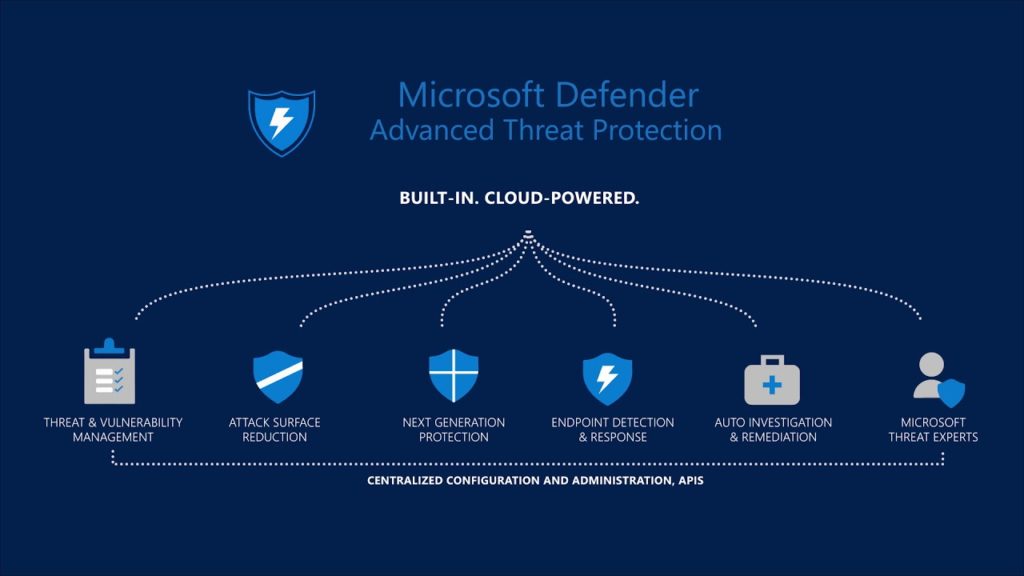
Windows Defender Antivirus creates the foundation for Microsoft Defender Advanced Threat Protection (MD ATP). Microsoft Defender ATP is antivirus on steroids. And just like steroids, it’s a juiced-up next-gen solution that’s only available via subscription. It adds the following feature set on top of the Windows Defender scan engine:
- Cross-platform support with MacOS
- Kernel level tracing
- Protection from fileless threats
- Threat and vulnerability management
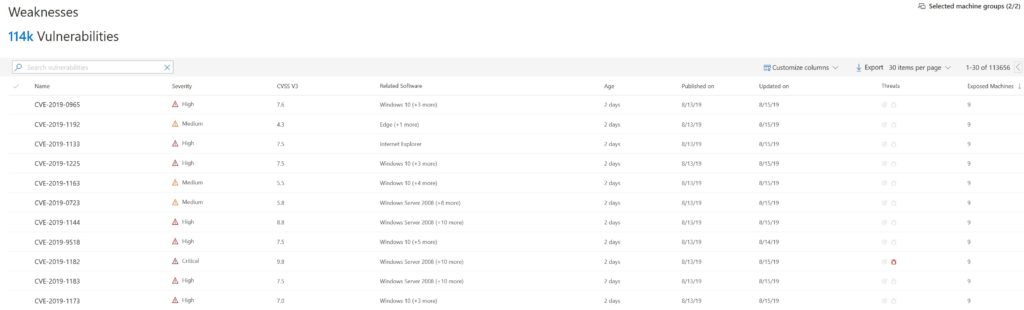
- I compared the CVE results with Tenable.io and let’s call it 99.9% the same. (Each solution found a single CVE that the other didn’t.)
- Microsoft Threat Experts for escalation to Microsoft’s world-class SOC and Cybersecurity Incident Response Team
- Threat intelligence correlation with other Microsoft security services via the Microsoft Intelligent Security Graph, which analyzes over 6.5 trillion daily signals
- Automatic incident investigation and response across all of your MD ATP connected devices using machine learning and AI
- Threat hunting and automation playbooks
- Endpoint detection and response (EDR)
- Centralized monitoring for your Managed Security Services Provider (MSSP) (That’s us!)
Microsoft Defender ATP combats the most sophisticated threats out there today through advanced technologies like behavioral analysis and machine learning. Another key benefit is device risk-profiling for conditional access.
Can your antivirus use a ransomware alert to automatically block you from accessing Office 365 and SharePoint?
Microsoft Defender ATP can.
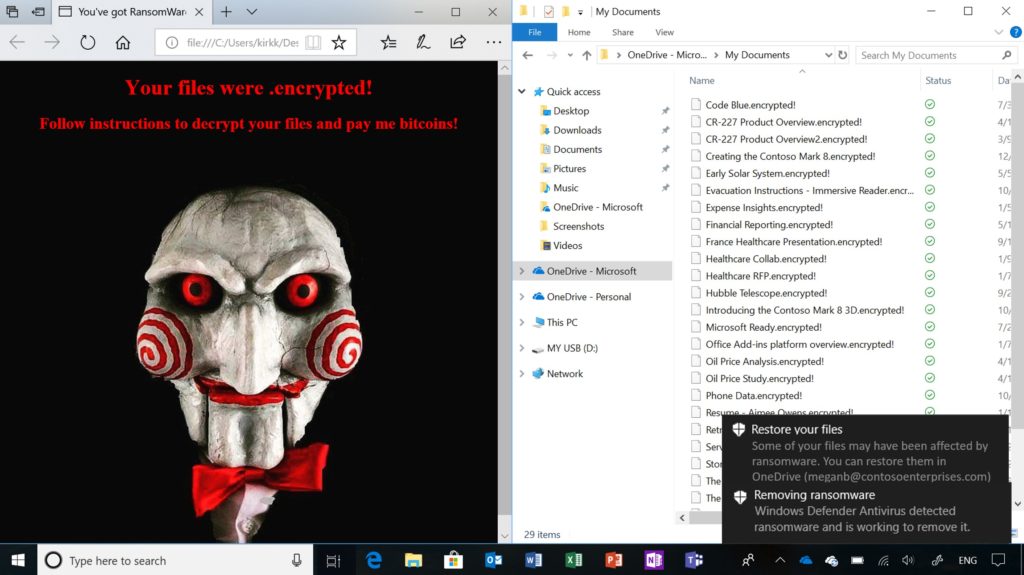
Yes, Mr(s). Smarty-pants, Microsoft Defender ATP can use device risk-profiling and conditional access to block you from accessing Office 365 before all your files are encrypted, not as a result of them being encrypted.
Threat and Vulnerability Management
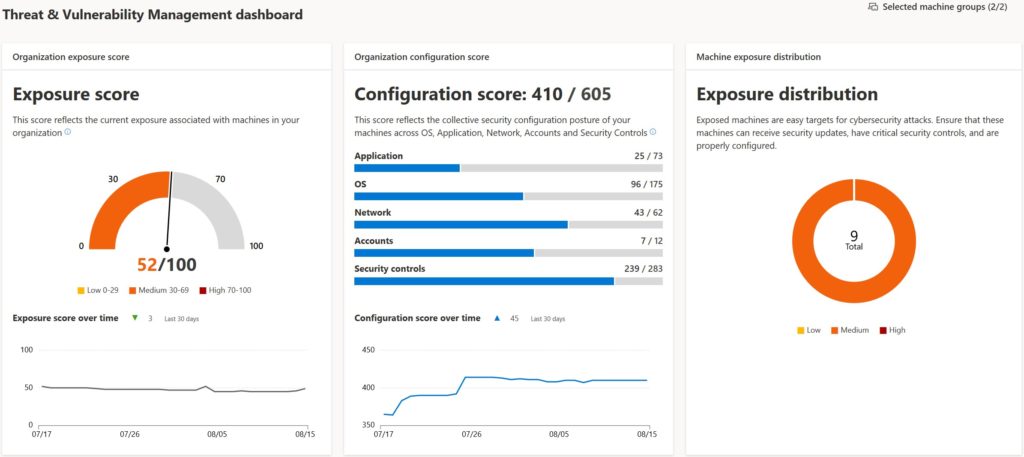
Now with the inclusion of vulnerability scanning in Microsoft Defender ATP, you can potentially eliminate your subscription to Nessus or Qualys credentialed CVE scanning. The Threat and Vulnerability Management (TVM) blade provides new capabilities like real-time detection and remediation guidance for any identified vulnerabilities.
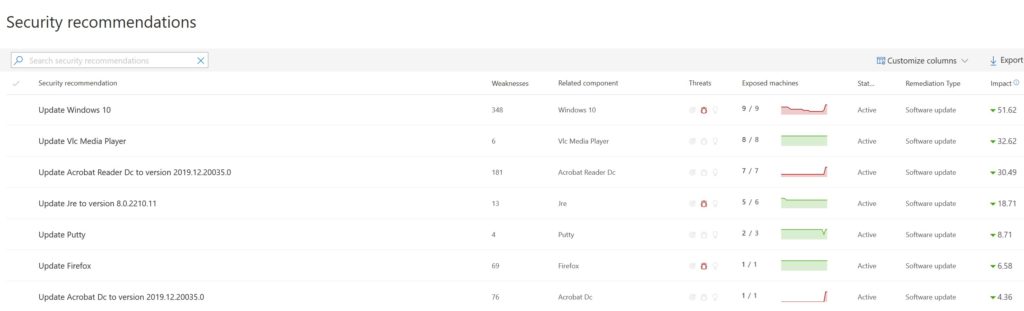
If your current MSP is using RapidFire Tools’ Network Detective or a similar dinky uncredentialed scanner, those are just toys and do not provide full visibility into your entire threat landscape. Uncredentialed vulnerability scanning is the equivalent of checking if the front door is locked, while completely ignoring that none of your windows have latches, your gas line is leaking, and your roommate is running a meth-lab in the basement. Any organization with NIST 800 / PCI-DSS / HIPAA / ISO27001 / etc. compliance must perform credentialed vulnerability scanning to prove compliance. </endrant>
For you gearheads, check out how Microsoft Defender ATP performs against MITRE’s ATT&CK Framework.
Microsoft Defender ATP for US Government GCC High Customers
Microsoft 365 G5 for government customers has been around since earlier this year, but it was missing a number of great features that are included with the commercial SKU. Fortunately, Microsoft Defender ATP for GCC High accounts is now available! However, Defender ATP is still missing a few commercial features, such as automatic investigations.
Check out the Microsoft website for the most recent list of available features in Microsoft Defender ATP for GCC High environments.
The Microsoft Security Response Center

The Microsoft Security Response Center (MSRC) was created over 20 years ago to engage with security researchers and rapidly repulse attacks against the Microsoft cloud. In 2019, the MSRC is staffed by more than 3,500 full-time security engineers, with their operations running globally in the Azure cloud. Microsoft continuously improves the commercial feature sets of its security products using research from the MSRC. This has translated into new product announcements this year, such as Azure Sentinel for SIEM and Microsoft Threat Experts for SOC escalation. Access to Threat Experts is only available with a Microsoft Defender ATP subscription.
The Microsoft Digital Crimes Unit
The MSRC also works closely with the Microsoft Digital Crimes Unit (DCU) to help protect all users on the Internet, not just Windows devices. The DCU helped identify nation-state actors that interfered in the 2016 election, including Strontium / Fancy Bear, and routinely assists with botnet takedowns. Here are a few examples from over the years:
- Rustock Botnet takedown in 2011 to block nearly half of global spam email
- ZeuS Botnet takedown in 2012 targeting digital theft of over $100 million
- Citadel Botnet takedown in 2013 targeting digital theft of over $500 million in 80 countries
- Ramnit Botnet takedown in 2015
- Andromeda takedown via disruption of Gamarue malware in 2017
- 99 Fake Iranian websites were taken down in 2019
Check out the latest news from the MSRC and DCU on their newsfeed: https://news.microsoft.com/on-the-issues/topic/cybersecurity/
Closing Thoughts on Windows Defender AV
If you want to avoid paying ransomware fees and suffering productivity loses, then Infused Innovations strongly recommends considering Microsoft Defender ATP with OneDrive Known Folder protection and Windows Autopilot. These three tools can either block a ransomware attack before it happens or allow you to recover from the attack within about an hour.
As for those of you that think Microsoft subscriptions are a form of ransomware, I’d still strongly encourage you to take a look at the free Windows Defender AV for your Windows 10 machines. Many of our clients that were paying for traditional antivirus have either upgraded to the next-gen Microsoft Defender ATP platform or switched to Windows Defender. Centralized management of the free tier of Defender is also possible using Dekstop Analytics (formerly Windows Analytics).
To reinforce our rationale for moving to Defender, the free version of Windows Defender AV outperforms numerous paid services, including:
- Avast Business Antivirus Pro Plus
- Bitdefender Endpoint Security
- ESET Endpoint Security
- McAfee Endpoint Security & Small Business Security
- Sophos Endpoint Security and Control
- Webroot SecureAnywhere
For the latest and complete anti-virus comparison results, head over to AV-Test:
Defender is now available for mobile endpoints too!
Have more questions about if Windows Defender or Microsoft Defender ATP is right for your organization? Check out this Whitepaper from Forrester on the Total Economic Impact of Microsoft Defender ATP or contact our sales team using the form below.
Im a break-fix shop moving into MSP. Currently using Solawinds RMM. What steps must I take to be able to offer Microsoft Defender Advanced Threat Protection rather than Bit Defender? From what I can see I need to become a CSP partner and then utilize InTune? Any insight/info greatly appreciated, thanks!
Sign up with TechData or Pax8 to become a Microsoft CSP provider. (Or we’d be happy to partner with you if you’d like.)
Onboarding for MDATP is just a PowerShell script. You can push it out through N-able if you’re licensed for Pro. (I would switch to Datto RMM though.) Intune is great for ongoing health attestation, but it’s not a requirement to deploy MD ATP. The devices just need to be Hybrid AADJ or cloud-only AADJ.