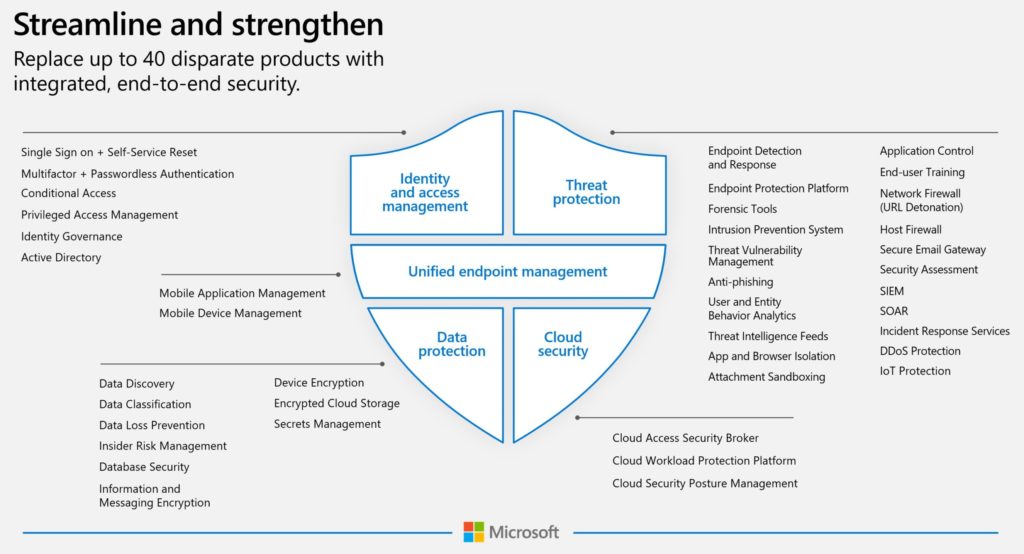
Building a Zero Trust Security framework with 20+ vendors has zero chance of success. This is why budgeting for Microsoft Defender XDR for Zero Trust Security must be at the forefront of a modern cybersecurity strategy for organizations of any size that are running Microsoft Windows or Office 365.
Microsoft Defender XDR allows you to consolidate over 27 security vendors into one integrated platform. That means one vendor for support calls, one single pane of glass to perform digital forensic analysis, and the entire suite is connected via the Microsoft Intelligent Security Graph. (Not to mention seamlessly built-in to the productivity suite that millions of you use every day.)
What is Microsoft Defender XDR?
Announced at Microsoft Ignite in 2020, Microsoft Defender XDR is a unified cyber defense platform that encompasses the entire Microsoft security stack. It spans both the Microsoft 365 E5 security products and what was previously called Azure Security Center. Many MD XDR services have been recognized by Gartner as industry-leading solutions. Some of the flagship products it includes are:
Microsoft 365 Defender
(previously Microsoft Threat Protection)
- Azure Active Directory Premium
- Microsoft Cloud App Security
- Microsoft Defender for Endpoints (previously Microsoft Defender ATP)
- Microsoft Defender for Identity (previously Azure ATP)
- Microsoft Defender for Office 365 (previously Office 365 ATP)
- Microsoft Endpoint Manager
Azure Defender
- Azure Defender for Servers (previously Azure Security Center Standard)
- Azure Defender for IoT (previously ASC for IoT)
- Azure Defender for SQL (previously ATP for SQL)
These products are available for both cloud-only and hybrid deployments. Using services like Azure Arc allows you to manage servers anywhere, whether it’s AWS, GCP, or on-premises including both physical boxes or virtual guests on Hyper-V, VMware, or Citrix.
One financial benefit of standardizing on the MD XDR stack is that all of the Microsoft 365 Defender logs are ingested into Microsoft Sentinel for free. For estimating additional log ingestion costs, visit our pricing guide for Microsoft Sentinel.
Attacker Kill Chain with Multiple Vendors
In this example, a desktop user opens an email containing malware. While the entire attack chain is covered, it requires seven vendors! The complexity of this security environment will lead to delays in detection time and a lack of automated response. Performing digital forensics across the entire attack chain will be a laborious, manual, and time-consuming process.
Attacker Kill Chain with Microsoft 365 Defender
The same attacker kill chain can be protected entirely with Microsoft 365 Defender. Each MD XDR product enhances the fidelity of the previous alert, creating a single incident in Azure Sentinel that covers the entire attack. Using the Security Orchestration Automation & Response (SOAR) and Automated Investigation & Response (AIR) tools inside of MD XDR, you can have an automated response triggered in seconds instead of hours.
Microsoft 365 Defender License Comparisons
Most likely, you will choose around three personas listed on our Complete Microsoft 365 Licensing Comparison so that you don’t have to purchase Microsoft 365 E5 for everyone. But let’s take a closer look at some of the different ways to get E5 Security without buying M365 E5.
Microsoft 365 E3
M365 E3 + E5 Security
M365 E3 + E5 Compliance
Microsoft 365 E5
Microsoft 365 E5 Security & E5 Compliance Add-ons
Microsoft 365 E5 Security
Microsoft 365 E5 Security is a must-have swiss army knife of security products, allowing for end-to-end visibility of attack chains for a user or device anywhere in the world. A brief overview of the features includes with Microsoft 365 E5 Security include:
- Azure AD P2 for risk-based conditional access.
- Microsoft Cloud App Security for SaaS session control policies and Shadow IT Discovery.
- Microsoft Defender for Office 365 P2 for email attachment and URL scanning.
- Microsoft Defender for Endpoint for next-gen Anti-Virus and device log-shipping to MCAS.
- Microsoft Defender for Identity for lateral movement and privilege escalation monitoring.
Microsoft 365 E5 Compliance
The Microsoft 365 E5 Compliance add-on will only be necessary in larger organizations or specific job roles for SMBs. For most SMBs, the basic eDiscovery and AIP functionality included with Microsoft 365 E3 will be sufficient. A brief overview of the features includes with Microsoft 365 E5 Compliance include:
- Advanced data governance for Data Loss Prevention on endpoints and Office 365.
- Advanced eDiscovery for legal and HR requests.
- Azure Information Protection P2 for automated file-level encryption.
- Customer Lockbox for restricting Microsoft support access to approved users.
- Information Barriers for regulatory separation of data within a single organization.
- Insider Risk Management for aggregating repeated DLP incidents associated with a specific user, or identifying potential data leakage from at-risk users.
Co-managed 24×7 SIEM with Azure Sentinel
A co-managed SIEM is where your log data resides in your Azure Tenant, and a managed security solutions provider (MSSP) correlates and triages your incidents. While Microsoft Defender XDR has plenty of built-in AI and automation, it’s not ready to detect sophisticated attacks, such as the SolarWinds supply chain attack. Human beings are still required to correlate incidents and hunt for threats.
Infused Innovations offers a globally staffed 24×7 Security Operations Center (SOC) that can assist with monitoring your Azure Sentinel environment and maturing your cybersecurity practice. US-based resources are available for organizations with strict regulatory compliance. Our pricing starts at $500/mo per 10 GB of logs, or $10/mo per device.
Microsoft Defender XDR Ninja Training Series
Beyond the security benefits of MD XDR, you can provide career path development for your internal IT team. The free resources at Microsoft Learn and Pluralsight offer employees pre-defined learning paths. Additionally, there are a few great “Ninja” training guides available too:
- Azure Sentinel Ninja Training
- Microsoft Cloud App Security Ninja Training
- Microsoft Defender for Endpoint Ninja Training
Closing Thoughts on Budgeting for Microsoft Defender XDR
A Zero Trust Security model integrates all available threat signals and assumes breach. Using a multi-vendor approach with zero trust security creates complexity, which can lead to data silos and delayed detection times. Microsoft makes it easy to adopt Zero Trust without having to look elsewhere. To assist with budgeting for Microsoft Defender XDR, take a look at the Total Cost of Risk Calculator to estimate savings against your current multi-vendor costs.
For folks that say “I don’t like the idea of putting all my eggs in one basket” keep in mind that many of the MD XDR security tools came from Microsoft acquisitions. Microsoft also invests $1 Billion a year in security R&D and employs over 3,500 cybersecurity engineers. (Which is larger than the entire employee counts at some of the alternative vendors, including their sales staff.)
If you are looking for a trusted Microsoft Gold Partner to assist with implementing Microsoft Defender XDR, Infused Innovations has the only end-to-end Zero Trust Security offer in the Azure Marketplace. Our Microsoft Defender XDR offerings are built on the following services:
- Deployment Services
- Zero Trust Security Accelerator for Modern Authentication
- Zero Trust Security Accelerator for Data & Device Protection
- Zero Trust Security Accelerator for Threat Detection
- Managed Security Services
- Infused Threat Protection for Users – phishing simulations, user training
- Infused Threat Protection for Devices – patching, monitoring, MDR
- Infused Threat Protection for 24×7 Co-managed SIEM
Interested in hearing more about our services? Fill out the contact form below!