Microsoft Defender for Endpoint and Intel TDT Combine for a New Ransomware Defense
Ransomware continues to be a growing and evolving threat. As some cyber attackers become increasingly sophisticated, things like ransomware kits allow even hackers with a low level of skill to take part in this malicious activity. With relatively little investment, they end up reaping big gains. And once that happens, they have all the more budget to develop new techniques and methods to further bait their targets. Publicly reported profits from ransomware and extortion attacks have shown a budget that rivals those of nation-state attack organizations—which means these ransomware attackers can operate very large-scale.
Microsoft and Intel have partnered to integrate Defender for Endpoint with Intel’s Threat Detection Technology (Intel® TDT), which can detect ransomware attacks at the hardware level. This technology will be available for consumers through Microsoft Defender Antivirus and will be enabled in Microsoft Defender for Endpoint later this year.
Intel Threat Detection Technology (TDT)
Ransomware encrypts business and user data, making it inaccessible to organizations in order to hold it for ransom—and this process creates a lot of activity in the target’s central processing unit (CPU). Intel TDT watches this activity through telemetry signals that its Intel hardware sends out. The hardware’s performance monitoring unit (PMU) records low-level information about the execution patterns of instructions that are processed by the CPU. This information then goes through machine learning techniques to help determine whether the CPU activity is legitimate or malicious. If an attack is happening, TDT is able to detect the malware code execution “fingerprint” at runtime.

Now paired with Microsoft Defender for Endpoint, the detector sends its signals to MDE, which applies its own threat intelligence and machine learning to assess the danger. If the occurrence is a true threat, Defender for Endpoint will automatically block or remediate it.
In addition to this new integration, Intel TDT has also recently added performance improvements and optimizations to its technology—for example, it now offloads the machine learning process to its integrated graphics processing unit (GPU), which allows for continuous monitoring.
WastedLocker Ransomware Example
The new Microsoft Defender for Endpoint and Intel TDT solution was tested with a family of ransomware called WastedLocker (or Win32). This ransomware, which first appeared in 2020 and continues to evolve today, generally lures users with fake browser updates that lead to the downloading of content that delivers the ransomware. Data is then encrypted and renamed with the extension “.eswasted.” These attacks are custom-configured to target specific organizations, and they are continually tuned to be able to evade security solutions.
Microsoft tested the most recent WastedLocker binaries on a PC deployed with Microsoft Defender for Endpoint and Intel TDT. When the ransomware was run, activity in the CPU during encryption could clearly be seen spiking:
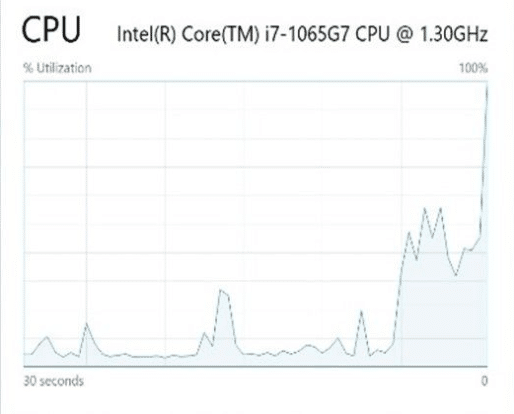
Graph from Microsoft
Then it was up to TDT’s machine learning as well as MDE’s threat intelligence to assess whether this spike was from normal usage or malicious activity. It identified the CPU activity as Win32, labeled it a severe threat, and automatically blocked it. It also created a notification of the threat with details about it.
Microsoft Defender for Endpoint and Intel TDT: Protection at Multiple Levels
With ransomware tactics constantly developing, security solutions need to evolve and become continuously better as well. The combination of Microsoft Defender for Endpoint and Intel TDT brings improved security at both hardware and software levels. This helps stop ransomware activity before it can do its damage. The result can be a huge saving in costs that would have been incurred for ransom payments, in addition to time and productivity lost. The integrated approach reflects a recognition of the need for well-rounded defense that covers multiple layers, bringing a stronger security stack to organizations.
More recent news in Microsoft security: