Start Moving to Modern Authentication
Microsoft has announced that it will end support for Basic Authentication in Exchange Online next year, on October 13, 2020. Various protocols will change their authentication methods, including Exchange Active Sync (EAS), Post Office Protocol (POP), Internet Message Access Protocol (IMAP), and Remote PowerShell (RPS) in Exchange Online. Applications that use any of these APIs/protocols will be moving beyond Basic Authentication and must sign in with modern authentication.

From Basic to Modern Authentication
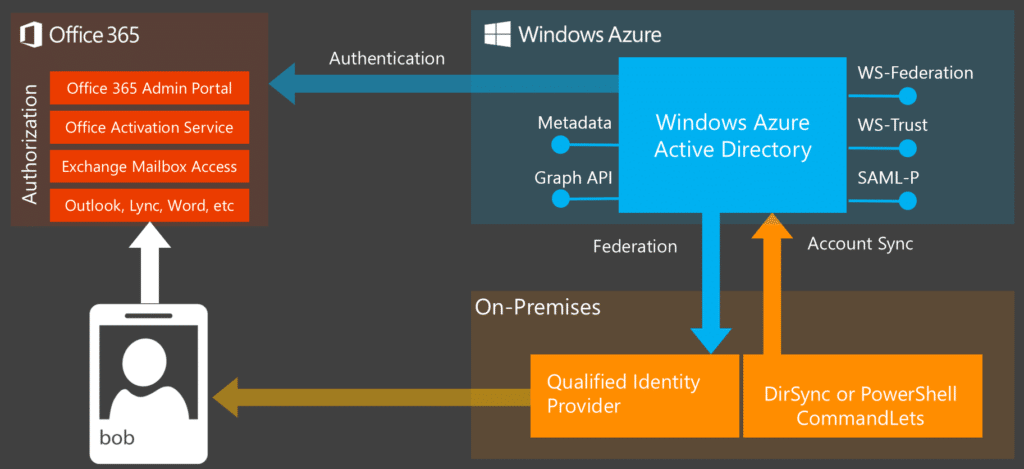
The tech industry has already started talking about moving beyond passwords to increase security through better credential methods. Basic Authentication is another term for the usernames and passwords that we’re so used to typing in. The trouble is, this method is too basic for today’s cyberspace. Attackers can easily target accounts by applying guessable passwords across an organization, and computers can generate password guesses very quickly. Microsoft is committed to moving beyond this Basic Authentication to Modern Authentication, which uses OAuth 2.0 tokens and the Active Directory Authentication Library. Modern also means multi-factor: it requires two pieces of evidence to prove a user’s identity. When these factors are biometric, accounts are much more difficult to attack. With the recent announcement, Microsoft will start shifting this change from a recommendation to mandatory procedure.
Basic Auth Will Still Work in Some Scenarios
Companies should note that this change only applies to Exchange Online–not on-premises versions of Exchange Server. (Although one might argue that “on-premises” is itself something that we should phase out.) It also does not affect SMTP AUTH; for now, Microsoft will continue to support Basic Authentication for it in Exchange Online.
Tips for moving beyond Basic Authentication smoothly
Microsoft admits that this will be a change that users will need to adapt to. They are working on improving OAuth 2.0 support for POP and IMAP, as well as background application support for Remote PowerShell MFA module. In the meantime, they recommend using Outlook Mobile clients to connect with Exchange Online. This can be a good choice for organizations that still use Exchange ActiveSync-based clients. Those who use remote PowerShell to connect to Exchange Online might consider switching to PowerShell within the Azure Cloud Shell. Since this version supports multi-factor authentication, it can help your organization get a head-start on modernizing.

For you hardcore PowerShell junkies, check out the PowerShell profile for connecting to Microsoft 365 services with MFA on GitHub that we use here at Infused Innovations.
Smaller organizations will have no problem moving to modern authentication. Larger organizations using third-party MDM solutions like MobileIron or MaaS360 to push managed email profiles to the native mail clients will have to rethink their mobile strategy. In an enterprise with thousands of users, this may be an expensive move that our cybersecurity experts can help you start planning now. To learn more, take a look at our blog post on modern authentication with Conditional Access.