What Are Decentralized Identifiers (DIDs)?
When you log into an account with Google or Facebook, you’re doing an identity verification through a central intermediary. While it may seem convenient to log in with these established accounts, it comes with concerns for privacy. These large intermediaries will gather metadata as you use the account—things like when and how long you used it, where you were located, and other online activity you engaged in during that time. This information is often used to create targeted ads for you. It can be surprising how quickly you start seeing ads for an item you looked up while your activity was being monitored. And ads seem relatively innocent when compared to other possible uses of this metadata, such as interference in elections. Decentralized identifiers (DIDs) provide a different credential-checking method that doesn’t rely on that intermediary.
How do Decentralized Identifiers (DIDs) Work?
DIDs are one of the components of self-sovereign identity (SSI), which allows for controllable and cryptographically secure identification without going through a third party. Instead of passing through a verifying intermediary like Google, DIDs are stored on an immutable blockchain. Individuals or organizations can create as many DIDs as necessary, which can be used in different contexts wherever identity verification needs to be done. There are dozens of different DID methods that can be used to create a decentralized identifier (the process does require coding—JSON Web Message is the standard format). Each DID is essentially a code, comprised of a scheme, a method, and a method-specific string:
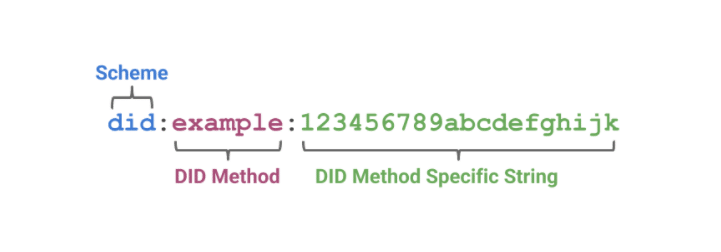
Example decentralized identifier from Affinidi
Once DIDs are created, parties can exchange them to create secure connectivity between them and confirm identification. Together with verifiable credentials (VCs), DIDs produce a trustworthy way to show proof of license where applicable.
What Types of DIDs are There?
Decentralized identifiers can be used in either public or private contexts. A public example is when a DID is used to issue a verifiable credential such as a passport. The identifier and credential are stored on a public blockchain ledger, so anyone can see them and verify that the owner has a right to travel internationally. One nice thing about verifiable credentials on such public ledgers is zero-knowledge proof, which means that the publicly accessible proof of license to travel does not necessarily show other information that would typically be on a physical passport, like place and date of birth. Only the proof itself is accessible. Furthermore, the blockchain cannot be changed and keeps a permanent record of who has accessed it, providing increased transparency.

The other type of DID is a private one which creates a secure channel that no third party has access to. So, unlike with the logins through intermediaries, no one is collecting metadata and using it to target you with ads or otherwise. Parties can use private DIDs as channels for communication or transmission of sensitive data without their use being monitored.
What Advantages Can DIDs Offer?
This secure digital identification is an alternative to a) physical identification cards and b) other (centralized) online credential processes. These are some of the improvements it can bring over those methods:
- In comparison to physical cards:
- Less stuff to pull out/fall out of a wallet
- Won’t get lost or stolen
- More control over which elements to share
- Less material waste
- Modernized online transmission (no need to scan and email)
- In comparison to centralized credential checking:
- No intermediary to go through
- No metadata collected
- More privacy
- Better control over one’s own data
Decentralized Identifiers for Secure Credential Transmission

As the marketing research group Forrester has said, “Decentralized digital identity (DDID) is not just a technology buzzword: It promises a complete restructuring of the currently centralized physical and digital identity ecosystem into a decentralized and democratized architecture.” By decentralizing the location of identifying data, power is taken away from big intermediaries and given instead to the data holders, or the people themselves. That’s a noble cause worth pursuing further. As it is right now, this us still a burgeoning practice. But as it becomes better known and more widely used, we may gain better control of our identifying information than we’ve ever had before.
For more on decentralized digital transactions, see our article on non-fungible tokens (NFTs).