What Are Verifiable Credentials?
In today’s highly digital world, we’ve come to rely on digital copies of documents. We keep and send digital files to reduce paper waste and speed up transmission. We store photos on hard drives or the cloud so we don’t have to print all of them, and those that are printed can always be duplicated if they get damaged. It makes sense to be able to have such digital copies of credential documents too. These are the items of proof that verify who we are and our license to do what we do: we’re old enough to get into a nightclub; we’ve earned a particular degree; we can be identified internationally for travel. Verifiable credentials allow for this digital copy to be stored and shared as needed, in a way that protects privacy even better than physical copies do.
What is the Verifiable Credentials Protocol?
The World Wide Web Consortium (W3C), which oversees international standards for the internet, created the verifiable credentials protocol. The goal was to make it possible to verify identity and credentials online in a way that is cryptographically secure and that respects privacy. It’s one of the three pillars of Self-Sovereign Identity, along with the Decentralized Identifiers protocol and Distributed Ledger Technology (also called Blockchain). These technologies work together to create a trustworthy and safe verification process that the ID holder has control of. A transparent record of use also keeps verifying entities accountable.

What Are Verifiable Credentials Composed of?
The most obvious component of a verifiable credential is its claim. For example, if the credential is your driver’s license, it claims that you’ve completed the requirements necessary to be allowed to drive. Along with that basic assertion is metadata that contains additional information: who issued the credential and when, the expiration date, a photo, etc.—as well as a public key that allows for verification. Finally, the credential holds proof of the claim: it verifies the source (or issuer) of the credential, that the license is still valid and hasn’t been revoked, and that the data is authentic and has not been tampered with.
What Are the Advantages of this Process?
As things are now, when we need to show proof of a credential over the internet, we typically scan and fax or email the physical card or document. Soon enough this will seem old-school, and for good reason: email can easily be hacked, and anyone who has a photocopy of your card has all the information on it that you do. You also have no knowledge of who might have accessed it maliciously, and no record of the legitimate parties who’ve gotten a copy over the years. With verifiable credentials, you have a record of when and where your information was shared, and you are able to revoke that relationship any time if you choose to. You can also pick and choose attributes that you want to disclose or keep private. For example, you can prove your birth year without giving away the month and day, or vice versa. There’s also no danger of getting verifiable credentials lost, stolen, or damaged like we have with physical copies.

How do Verifiable Credentials Work?
The elements of credentials that verifiers will access are stored on a tamper-proof ledger (or blockchain) in decentralized databases—instead of going to the issuer itself, a verifying party will get the information through this cross-referenced blockchain. What’s most interesting is that the ledger doesn’t actually store the data itself, but rather the signatures and attestations to it that are necessary for verification. This capability is known as zero-knowledge proof. Since the ledger is immutable, the information on it can’t be changed and actual personal data shouldn’t be stored on it. Different types of credentials have particular schemas that issuers or verifiers use to keep the process standardized.
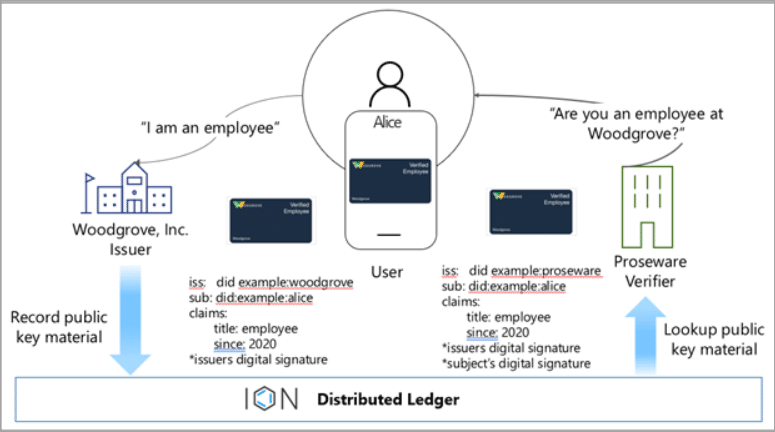
Example process between issuer, holder, and verifier (courtesy of Microsoft)
To illuminate the process, let’s continue with the driver’s license example. The issuer, the DMV in this case, publishes its own decentralized identifier (DID) on the blockchain ledger as well as a schema which outlines what information is in a driver’s license (name, DL#, address, etc.). When the DMV issues you your verifiable credential, you hold it in your own DID “wallet” and control how much you want verifiers to see. If a police officer pulls you over and wants to see your driver’s license, you can share just the digital signature which verifies that you are allowed to drive, without sharing the actual data or specific information. The officer won’t be able to see your address or birth date. But if your license expires, the DMV can publish that on the blockchain and police will be able to see the update, since it’s relevant to your license to drive (which is what the officer needs to verify).
What Do these Verifiable Credentials Look Like?
In terms of user visuals, these will look like cards in a digital wallet. They can be accessed through web or mobile versions which provide a simple and familiar type of experience. Their design can be customized, for example by the administrators of a business that uses them for employee verification and wants to reflect their company style and branding.
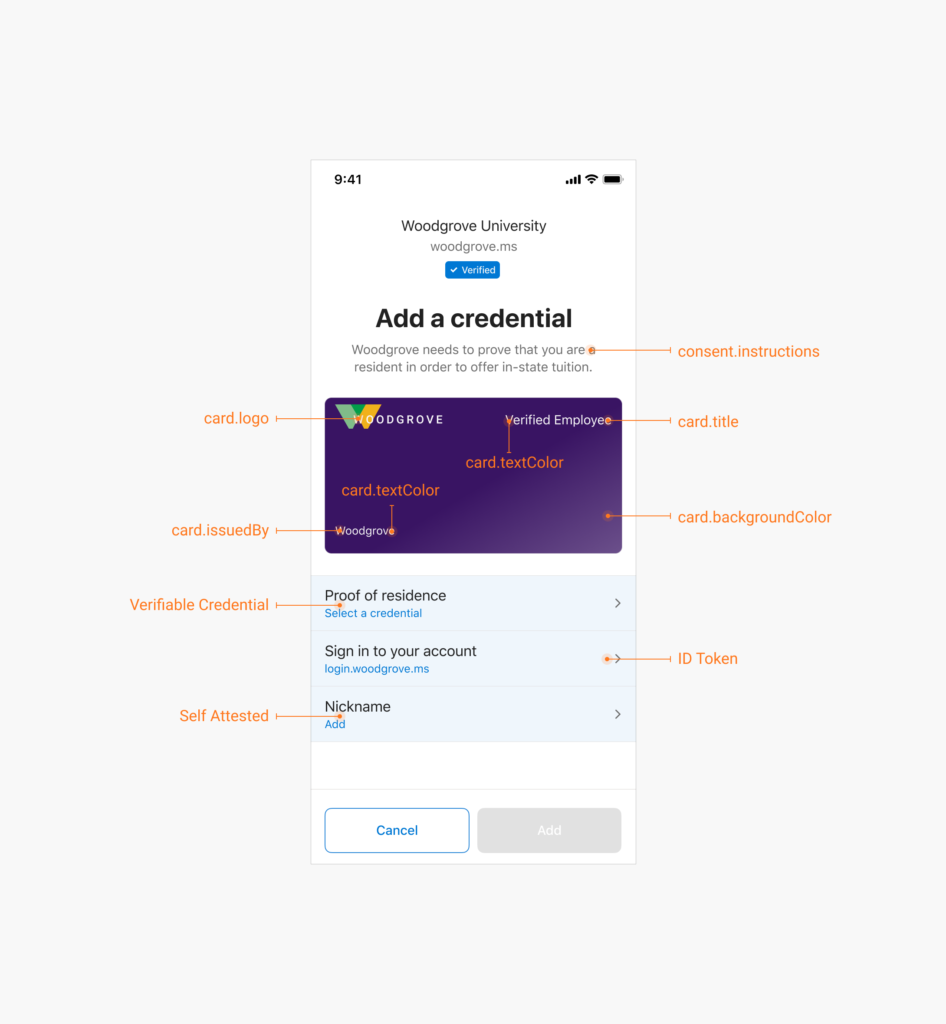
Example credential customizing in Azure AD Verifiable Credentials, now in preview.
Verifiable credentials are a modern, convenient, and secure way to store and use identifying documents. With capabilities that aren’t possible in physical copies, they allow for private and controlled verifications.
Interested in who designs these cards? Check out this interview with Frank Chiachiere, a former theater actor who now designs user interfaces for verifiable credentials.