Create Your Zero Trust Business Plan
The recent Solarigate news has many of us chilled and concerned about how to protect ourselves and our organizations. It's clear that we can't take cybersecurity for granted and we can never be too careful with our data and networks. That's why we strongly recommend adopting a Zero Trust policy. Within this type of security framework, trustworthiness is never assumed and the utmost care is put into tight cybersecurity. But Zero Trust can be confusing and a bit tricky to set up and get running, especially if this type of security standard isn't what you've done in the past. Now Microsoft has developed a Zero Trust Business Plan document to help guide you through the process that will best strengthen your company's cybersecurity.
Zero Trust Principles

Zero Trust is a philosophy and practice that is meant to extend throughout an organization, integrated into the entire cybersecurity strategy. There are three main guiding principles that you want to follow in a Zero Trust framework:
- Verify everything explicitly. Authenticate and authorize every time, based on every available data point.
- Grant access by least privilege. Allow access to data only to those who need it, when they need it. Access can be limited through data protection and risk-based adaptive policies, and with Just-In-Time and Just-Enough-Access (JIT/JEA).
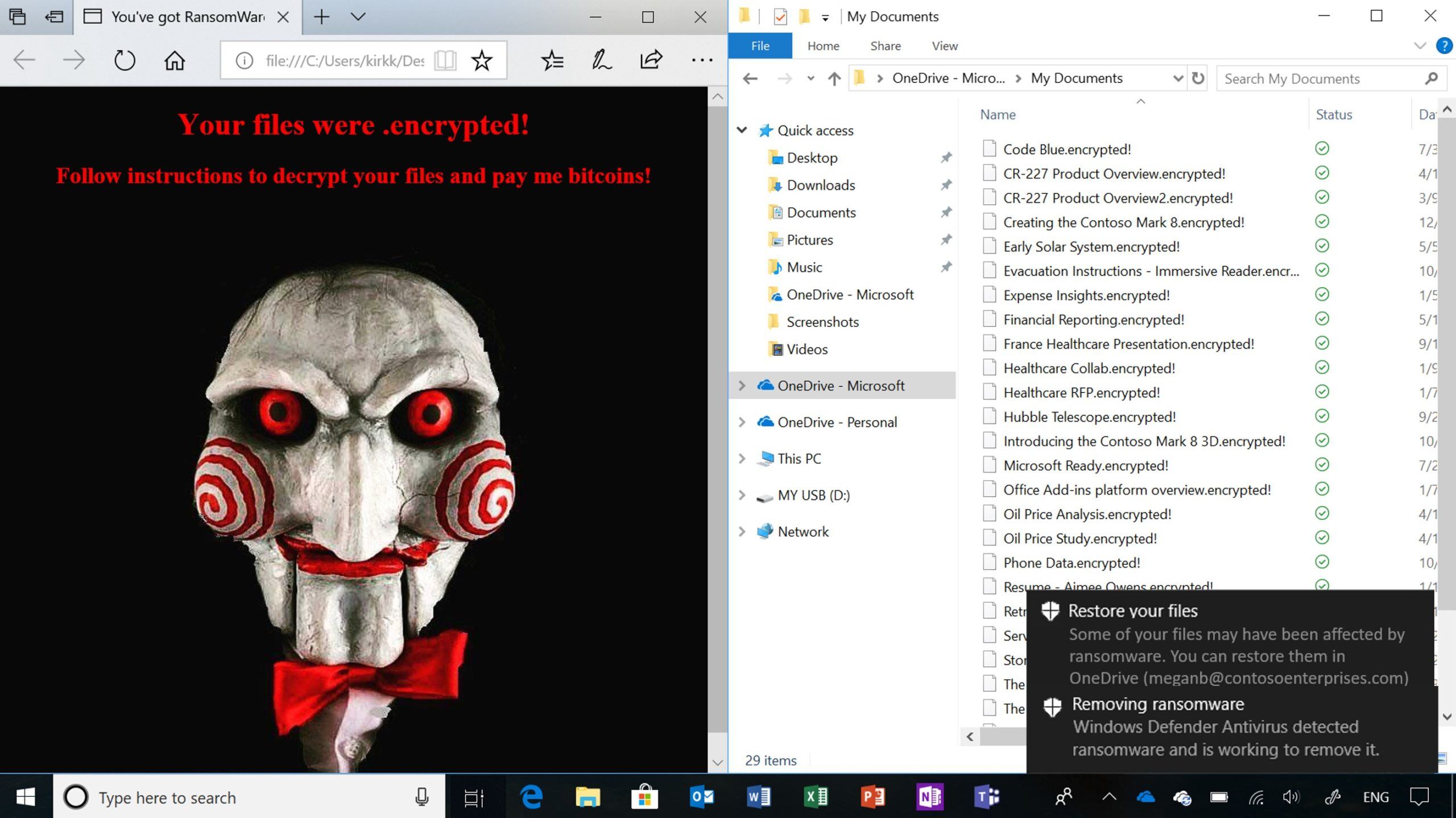
- Assume you're breached. As we've written regarding the supply chain attack on SolarWinds, the best line of defense against such an attack is to assume you're already breached, or that you will be soon. This shifts your mentality out of complacency and into defense mode. You want to gain visibility, verify end-to-end encryption, and create layers of security that limit the impact of an attack.
Microsoft's Zero Trust Business Plan
Microsoft just released their Zero Trust Business Plan document, which provides guidance through the life cycle of implementing and carrying out a Zero Trust initiative. It features insights from business leaders who have integrated Zero Trust into their own organizations' security strategies. In it you can find tips on how to plan, implement, and measure the success of your process. What does a good strategy look like? What kinds of milestones should you shoot for? How can you measure security effectiveness? If you're new to Zero Trust and want to get started or become more acquainted with it, this document is a straightforward, fairly quick read to get you pointed in the right direction.
More Zero Trust Guidance and Resources
Microsoft also provides additional help with Zero Trust to aid organizations in building a plan and making the best use of what the framework has to offer:
- Their Zero Trust Deployment Center details the core elements of the approach and provides steps on how to optimize implementation. It contains further links on how to use Zero Trust to secure identity, endpoints, applications, data, infrastructure, and networks. It also explains how you can use visibility, automation, and orchestration to "move away from a trust-by-default perspective to a trust-by-exception one."
- Think you're already on the right track, but not sure you're all the way there? You can take a Zero Trust Assessment test that will help you see where you're at. Every organization is unique, and depending on what technologies you're using and any requirements of your field, your journey may look different from others'. This assessment tool can help you pinpoint what needs to be done and provide recommendations on how to best move forward.
And, as always, we are happy to give you guidance and answer questions as well. Send us a message and let's chat Zero Trust!
Stay connected. Join the Infused Innovations email list!
Share this
You May Also Like
These Related Posts
Top 10 Security Best Practices with Microsoft 365 in 2021

Let's Face It: Passwords Aren't Secure Enough for Your Business
No Comments Yet
Let us know what you think