10 Ways to Use Microsoft 365 for Campaigns in 2020

As we near this year's U.S. presidential election, one big concern on people's minds is whether the process will be secure and free from outside interference. Microsoft has responded to this concern with its Defending Democracy Program, its most recent development being Microsoft 365 for Campaigns. This is a simple and powerful service meant for those who need to focus their energies on campaign goals. The service is available to anyone working within a federal campaign or on a national committee in the United States. It's crucial for campaigns to be vigilant and ensure they are not vulnerable to cyber interference, and Microsoft 365 for Campaigns is a great way to do that.
Top ten cybersecurity recommendations in Microsoft 365 for Campaigns
So how can staff make use of Microsoft 365 for Campaigns? These are campaign security recommendations from Microsoft's own Senior Cybersecurity Strategist Ethan Chumley:
- Use two-factor authentication for all campaign staff.
- Train staff on how to identify phishing attacks quickly.
- Be sure administration has dedicated accounts.
- Increase malware protection in email.
- Set up good protection against ransomware.
- Block emails from auto-forwarding outside of the campaign.
- Increase encryption for emails with sensitive information.
- Apply Advanced Threat Protection (ATP) anti-phishing to guard email accounts from phishing attacks.
- Protect email from malicious attachments with ATP safe attachments.
- Defend your email against phishing attacks with malicious website links with ATP safe links.
Two-factor authentication
You've already seen this all over the place--it's what's going on when you get a verification code on your phone in order to access an account on your computer. It simply adds another level of security, and that goes a long way in protection. Security is also moving toward modern authentication with biometrics rather than passwords, a change that would drastically reduce the vulnerability of campaigns. Those using Microsoft 365 for Campaigns should turn on multi-factor authentication (MFA) and require it from both admins and other users.
Training staff to identify phishing attacks
It's important for campaigns to establish threat awareness across the board. Cybersecurity should be something all staff know about and have at the top of their minds. Train them to be wary of suspicious messages. For guidance on how to create a "culture of information security awareness," take a look at Harvard Kennedy School's Cybersecurity Campaign Playbook.
Dedicated administration accounts
Since admin accounts have elevated privileges and more access to sensitive information, they are at a higher risk of attack. Admins should use these accounts only when doing administrative tasks, and use separate regular accounts during other times. Before using an admin account, close all personal accounts and unrelated browser sessions. Once the admin tasks are finished, be sure to log out of the admin account.
Malware protection for email
Certain file types are commonly used for malware. You can increase the protection already included in Microsoft 365 by blocking attachments with these file types. You can do this quickly by going to the Office 365 Security & Compliance Center: under Threat Management, choose the Anti-Malware policy and turn the Common Attachment Types Filter on.
Ransomware protection
Ransomware works by encrypting files and locking computer screens, and holding data for ransom. Here are two mail flow rules you can implement to increase your protection from ransomware:
- Warn your users to carefully check file types in attachments. Uncommon or unknown file types (such as dotm, docm, xlsm, sltm, xla, xlam, xll, pptm, potm, ppam, ppsm, or sldm) should not be opened. Also, do not open any attachments that include macros from unknown senders.
- Block file types that could contain ransomware or malicious code. (These include ade, adp, ani, bas, bat, chm, cmd, com, cpl, crt, hlp, ht, hta, inf, ins, isp, job, js, jse, lnk, mda, mdb, mde, mdz, msc, msi, msp, mst, pcd, reg, scr, sct, shs, url, vb, vbe, vbs, wsc, wsf, wsh, exe, and pif.)
Blocking email auto-forwarding
Hackers who do get access to an account send information out by auto-forwarding emails. You can block this capability by creating a mail flow rule in the Exchange admin center.
Increasing encryption
Office Message Encryption is already included in Microsoft 365, so be sure to make use of it. To send an encrypted message in Outlook, go to Protect > Change Permissions > Encrypt. If the recipient is using Outlook 2013 or Outlook 2016 and Office 365, they'll see an alert about the restricted permissions and will still be able to read it. If they're using a different email provider, they'll see a link that allows them to sign in to read the message or request a one-time pass-code to view it.
Protection from ATP anti-phishing
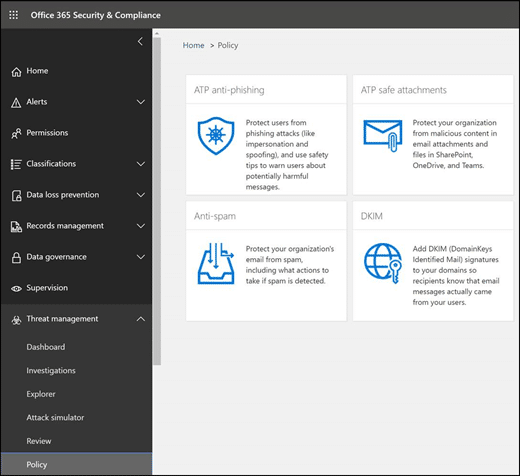
ATP anti-phishing protection is part of Office 365 Advanced Threat Protection. It helps protect against malicious and impersonation-based phishing attacks. This recommendation only applies if you've configured a custom domain in Office 365 or Microsoft 365. If you have, set up ATP anti-phishing for your custom domain under Threat Management in the Office 365 Security & Compliance Center.
Enabling ATP safe attachments
This is one more step in guarding against malicious emails. ATP Safe Attachment is a helpful tool within Office 365 Advanced Threat Protection--but it isn't turned on by default, so be sure to enable it. You can also do this under Threat Management in the Security & Compliance Center. Emails with suspicious attachments will be quarantined.
Using ATP safe links
Hackers often put malicious websites into email links. ATP safe links provides time-of-click verification of the URL that a link directs to and protects you from going to a malicious site. You should increase protection from the default policy on this, and also add a new policy targeted to all recipients in your domain.
Microsoft Secure Score
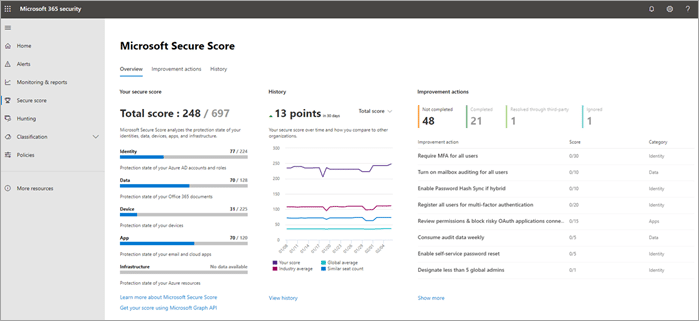
You can check how well you're doing all of this with a Microsoft 365 Secure Score in the Microsoft 365 Security Center. It will basically assess your security and give you a score. This makes it easier to gain insights and make improvements.
Guidance in using Microsoft 365 for Campaigns
For more detailed information on how to implement these protections, see this guide from Microsoft. Our article on AccountGuard also provides insight on the Defending Democracy Program and campaign resources.
Stay connected. Join the Infused Innovations email list!
Share this
You May Also Like
These Related Posts
The Future is Now: How AI and Robotics Can Help Fight Disease

Tech Trends We Can Expect in 2021

No Comments Yet
Let us know what you think