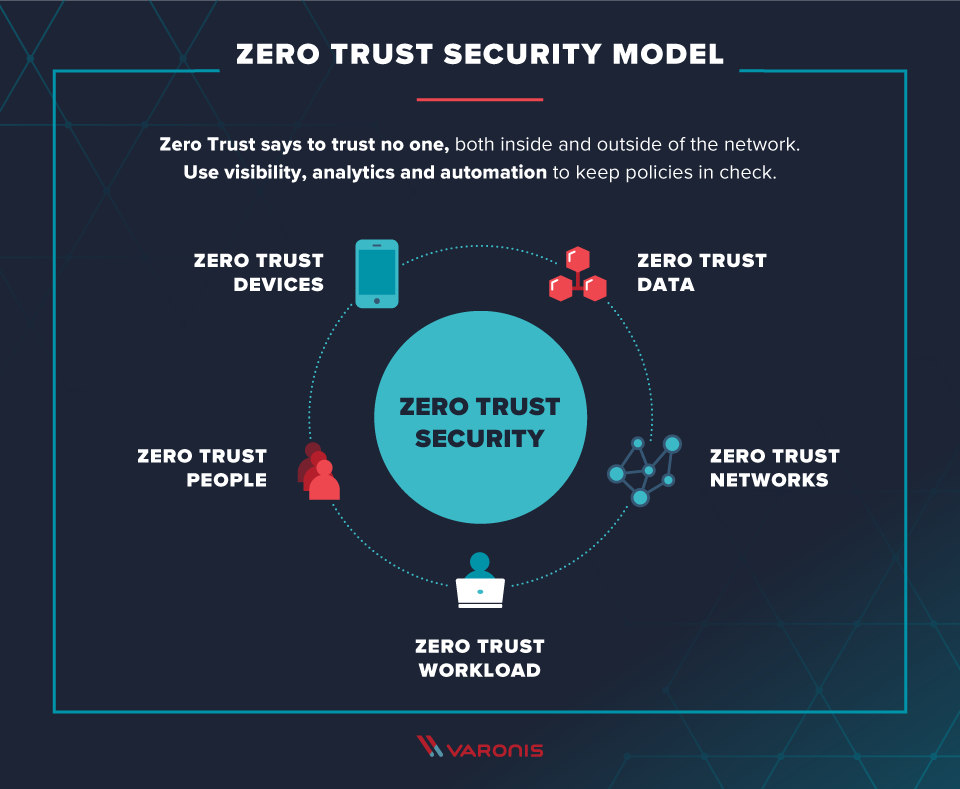
Pros and Cons of the Zero Trust Model
The Zero Trust model is a security framework that operates like its name suggests: it follows the policy of trusting no one, including those within the network. Every entity (inside or outside the network) is assumed to be a potential threat and should not be considered safe until it is checked and verified. Thus, every device and user in an organization must be monitored and managed. This strict security practice has its pros and cons, which we'll go over.
How Zero Trust came about
The concept of the Zero Trust model was started in 2010. John Kindervag, then Vice President and Principal Analyst for Forrester Research, came up with the idea when considering weaknesses in the traditional security model. That traditional model assumed that entities inside the network could be trusted. While that may generally be an instinctive assumption, it leaves room for vulnerability. Kindervag considered this assumption outdated as technology advanced and cyberthreats became more of a problem. He inverted the model to view everyone as "guilty until proven innocent." While insider threats are not something organizations necessarily expect, they operate on the safe side and require verification everywhere. Ever since Kindervag originally came up with the concept, businesses have increasingly chosen to apply this model in their security plans. In 2018, one Forrester analyst said 17 out of 20 calls he got were about Zero Trust---and the framework is even more relevant today.
Advantages of using the Zero Trust Model
Should you incorporate this framework into your company's security practices? Building a Zero Trust network is a considerable task, but sometimes it's worth it to put the extra effort in. Let's look at some pros and cons to help you decide whether a Zero Trust model is right for you.
Here are some strengths of the Zero Trust model:
- Less vulnerability. Once in place, the Zero trust model better secures the company, especially from in-network lateral threats that could manifest under a different security model.
- Strong policies for user identification and access. Zero Trust requires strong management of users inside the network, so their accounts are more secure--making the entire network more secure. Using multi-factor authentication or even moving beyond passwords with biometrics is a good way to keep accounts well guarded. Then, with the categorization of users, they can only be granted access to data and accounts as necessary for their particular job tasks.
- Smart segmentation of data. In a Zero Trust model, you wouldn't have one big pool of data that all users could access. Segmenting data according to type, sensitivity and use provides a more secure setup. This way, critical or sensitive data is protected potential attack surfaces are reduced.
- Increased data protection. Zero Trust also keeps data well guarded in both storage and transit. This means things like automated backups and encrypted or hashed message transmission.
- Good security orchestration. This is the task of making sure all your security elements work together efficiently and effectively. In an ideal Zero Trust model, no holes are left uncovered and the combined elements complement one another rather than presenting incongruities between them.
Challenges of using the Zero Trust Model
With all these additional security strengths, the Zero Trust model does make a security policy more complicated. Here are some of the additional challenges that come with such a comprehensive strategy:
- Time and effort to set up. Reorganizing policies within an existing network can be difficult because it still needs to function during the transition. Often it's actually easier to build a new network from scratch and then switch over. If legacy systems are incompatible with the Zero Trust framework, starting from scratch will be necessary.
- Increased management of varied users. Employee users need to be monitored more closely with access only granted as necessary. And users can go beyond employees. Customers, clients and third-party vendors may also use the company's website or access data. This means there's a wide variety of access points, and a Zero Trust framework requires specific policies for each type of group.
- More devices to manage. Today's work environment includes not only different kinds of users, but several types of devices for each of them. Different devices may have their own properties and communication protocols which must be monitored and secured specific to their type.
- More complicated application management. Likewise, applications are varied. Apps are often cloud-based with use across multiple platforms. They may be shared with third parties. In line with a Zero Trust mentality, app use should be planned, monitored and tailored specifically to user need.
- More careful data security. These days there's more than one location data is stored, which means there are more sites to protect. Data configuration needs to be done responsibly with the highest security standards.
Closing thoughts on the Zero Trust model
As you can see, the cons of using the Zero Trust model are mainly related to the additional work required to implement it. It is a strong security framework--it just takes a good amount of effort to set up. Without assumed trustworthiness, the network is more secure. If the company does get penetrated by a cyberattack, the virus can't move laterally throughout the network since that movement is also regulated. So this comprehensive, specified approach is a good idea in security terms. The question is whether and how your company is able to switch over to it. One Zero Trust foundation we recommend is Microsoft Azure AD---we even have a guide for setting it up there.
For more on security related issues, read our blog about why ransomware is still a problem.
Stay connected. Join the Infused Innovations email list!
Share this
You May Also Like
These Related Posts
Microsoft Announces Zero Trust Implementation Partnership with Infused Innovations
No Comments Yet
Let us know what you think