Shared Responsibility Matrix for Cloud Services
When migrating to the cloud, organizations sometimes mistakenly assume that the cloud service provider (CSP) takes on the role of securing their data and maintaining compliance. While the CSP does have many responsibilities in these areas, it's important to remember that the customer is also responsible. The service model you choose dictates your accountability in the shared responsibility matrix for cloud services. Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) provide increasing CSP support respectively. The diagram above outlines the increasing responsibilities of the CSP across each of these platforms. In real-world terms, this translates to cloud datacenters with military-grade security as seen in the following video.
In a traditional on-premises setup, the customer is responsible for all of its own management and security. Depending on the desired level of support from the CSP, an organization can choose whether to use an IaaS, PaaS, or SaaS. So the next time someone tells you that on-premises is cheaper, make sure they're including the cost of 24x7 armed guards, HDD destruction policies, three days of backup power, and the rights to diesel reserves immediately behind the hospitals in the event of an extended power outage.
Controls, Evidence, and Compliance Obligations
No matter which model the organization uses, it is still responsible for compliance obligations. This means that it must securely identify and classify its own company's data to meet compliance standards. The customer is in charge of distinguishing between sensitive material and what is publicly accessible. If these tasks are challenging, Microsoft's paper on how to classify data to be ready for the cloud is helpful. Additionally, there are a number of third-party vendors that can assist with your comprehensive security policy documentation.
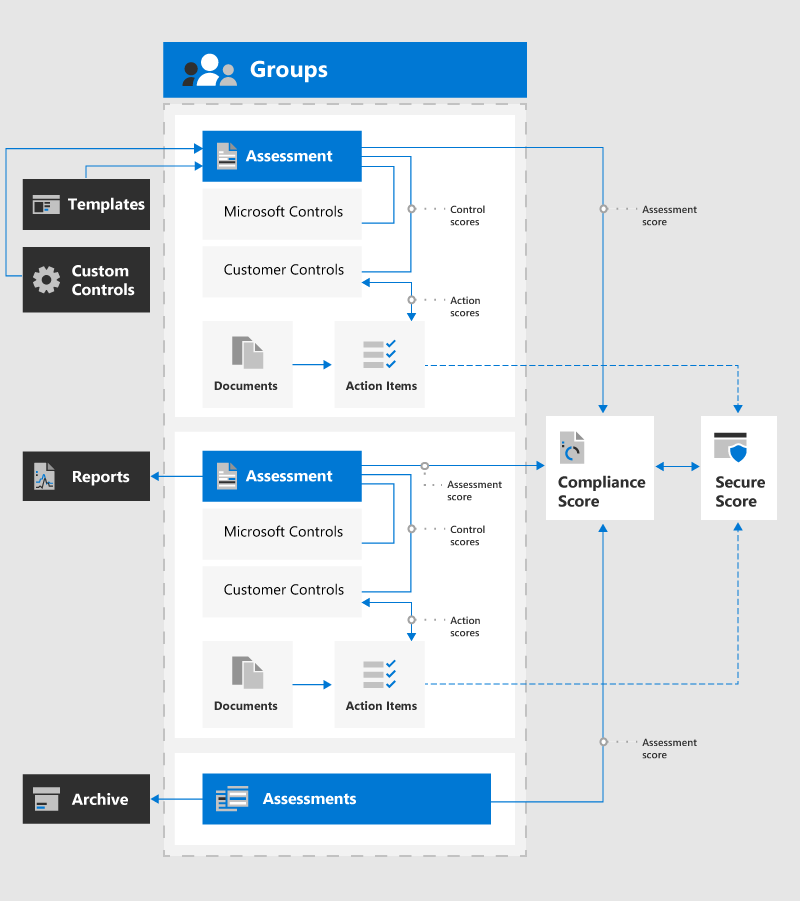
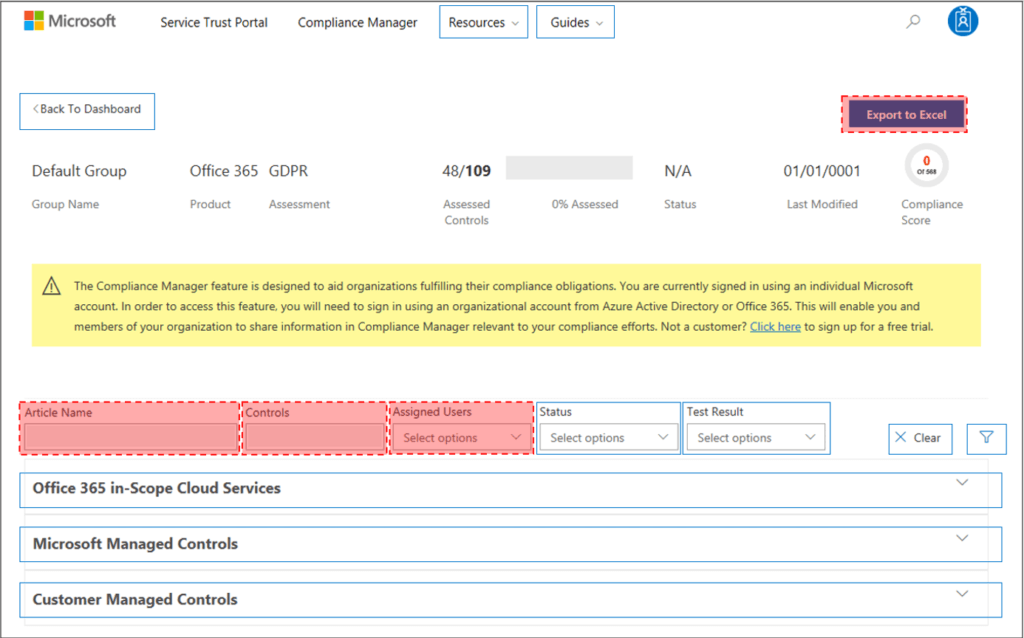
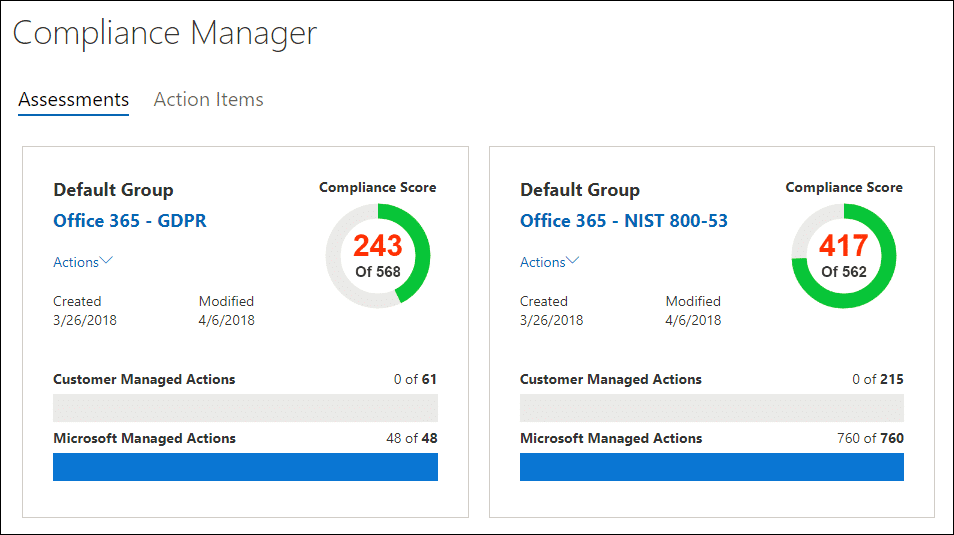
Compliance Manager for Shared Security Controls
Microsoft's Compliance Manager streamlines the process of identifying which controls are the responsibility of the customer. Then it also allows you to assign controls to employees to complete. The following compliance frameworks are natively built into Compliance Manager:
- ISO 27001:2013
- ISO 27018:2019
- NIST 800-53
- NIST 800-171
- National Institute of Standards and Technology Cybersecurity Framework (NIST CSF)
- Cloud Security Alliance (CSA) Cloud Control Matrix (CCM) 3.0.1
- Federal Financial Institutions Examination Council (FFIEC) Information Security Booklet
- HIPAA / HITECH
- FedRAMP Moderate
- European Union GDPR
Client and Endpoint Protection
With the use of many different devices within an organization, it's crucial to set clear boundaries when they connect to the cloud service. A service such as Microsoft Intune can help with secure device management. But this is still an area that is primarily under the responsibility of the customer--it's their job to keep accountability for their own users. By enrolling devices with Intune, you can continuously audit device health attestation and block uncompliant devices from access.
Identity and Access Management
User management and access need to strike the best balance between security and user convenience. Some like to think of it as managing who can do what. At Infused Innovations, we believe that conditional access with MFA works better together to achieve this balance.
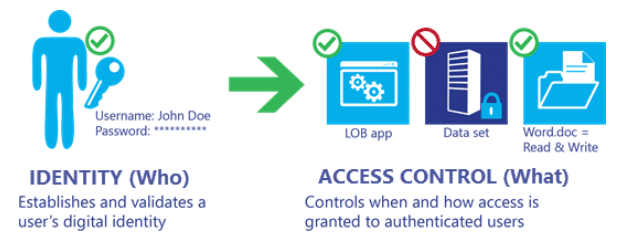
A similar question is who (CSP or customer) does what in terms of managing these controls. In IaaS, the customer is still responsible for setting them. In PaaS and SaaS, this management is a collaboration between the CSP and the customer. The organization will need to create an implementation plan configuring user identities and administrative services, and detailing how service access controls should be implemented. The CSP can then manage user access accordingly. Azure Active Directory can aid in identity management with two-factor authentication and role-based access control (RBAC).
Application Control
Similarly, platform-managed applications provide stronger support from the CSP. The customer will still need to correctly configure the services, but then the CSP steps in with comprehensive security and can even integrate this with identity management. Again, those with IaaS will need to take more responsibility for protecting the operating system and application layers of their virtual machines. This includes credentialed CVE scanning, machine policies, reflexive firewall rules, and SIEM for behavioral monitoring.
Network Control
This relates to how services communicate and operate together. Controlling network elements means configuring, managing and securing things like DNS, load balancing, and gateways. Here we have a greater responsibility for the CSP in both PaaS and SaaS. For SaaS solutions, this is a core benefit of what the provider offers. The CSP takes care of most of this in PaaS solutions as well, although customers can configure network-level services in an Azure Virtual Network.
Host Infrastructure
"Host" includes platform, compute and storage services. (Think virtual hosts, service fabric, containers, CDN, file storage.) The CSP will operate these services in the PaaS and SaaS models. In an IaaS setup, the customer will need to be familiar with the management and security of virtual machines. This includes the categories above as well as patching and operating system configuration.
Physical Security
A big part of the reason organizations choose to move to the cloud is the physical security it offers. Indeed, this is the primary difference between data on-premises vs. in the cloud. All of the cloud service models remove the customer's responsibility for buildings, facilities, servers and networking devices. The CSP ensures that buildings are physically secure, power is continually maintained, and backup locations allow service to continue in the event of a natural disaster. Air quality and cooling of equipment are also factors that the CSP will regulate.
Closing Thoughts on the Shared Responsibility Matrix for Cloud Services
It should be clear that customers who want less responsibility overall should opt for a SaaS solution. Here the CSP takes care of the bulk of application and underlying components. PaaS solutions present more of a balanced responsibility, with customers in charge of managing and securing applications, identity, clients and data. IaaS solutions require the customer to handle these things as well as the operating system and network configuration.
In all cases, customers must protect their users, classify their data well and make sure they are operating under SOC2/HIPAA/PCI compliant standards. The cloud service provider will do its job--but as in any partnership, both sides need to recognize their shared responsibility for cloud services for the platform to be secure and compliant.
Stay connected. Join the Infused Innovations email list!
Share this
You May Also Like
These Related Posts
Microsoft Defender for Cloud: the Only Offering that Natively Supports Azure, AWS, and Google Cloud

Compliance Comparison of Remote Assist Apps with MCAS

No Comments Yet
Let us know what you think