Using Zoom? You Just Failed Your Compliance Audit
Have you been on a Zoom group call recently? I have---not for work, but my kids' school class has done online show-and-tell over Zoom, and my extended family has organized virtual gatherings with it. Schools and universities use it as their go-to platform for online teaching. Friends are using it for happy hour meetups. And, as you may have heard, graduate students are defending their dissertations there---and being interrupted with hackers' pornography and hate speech.
The blatant disregard for fundamental security practices in Zoom's non-existent Security Development Lifecycle have led to Zoombombings and unsecured meeting scraping tools. But it doesn't stop there. Zoom also violates data sovereignty and data protection policies that are present in every cybersecurity framework (NIST CSF / HIPAA HITRUST / PCI-DSS / ISO27001) and consumer privacy laws such as CCPA and GDPR. Third-party risk management must be sacrosanct for all organizations, and Zoom is failing its customers across the board. School districts in New York and aerospace industries have started banning zoom because of security issues, and your organization should too.
Security Weaknesses in Zoom
Rather than using existing encryption standards for voice and video content, Zoom creates its own. Our CISO, Dan Chemistruck, says that "unless you have a dedicated security research lab, like Apple or MIT, this is an open invitation to hackers to breach your platform." Zoom's security methods consist of "transport" encryption between servers and devices---not end-to-end encryption. Until very recently Zoom misled users to believe that its encryption was end-to-end. After the news reports of hacking incidents last week, Zoom representatives apologized in a blog post on April 1 for the "discrepancy between the commonly accepted definition of end-to-end encryption and how we were using it."
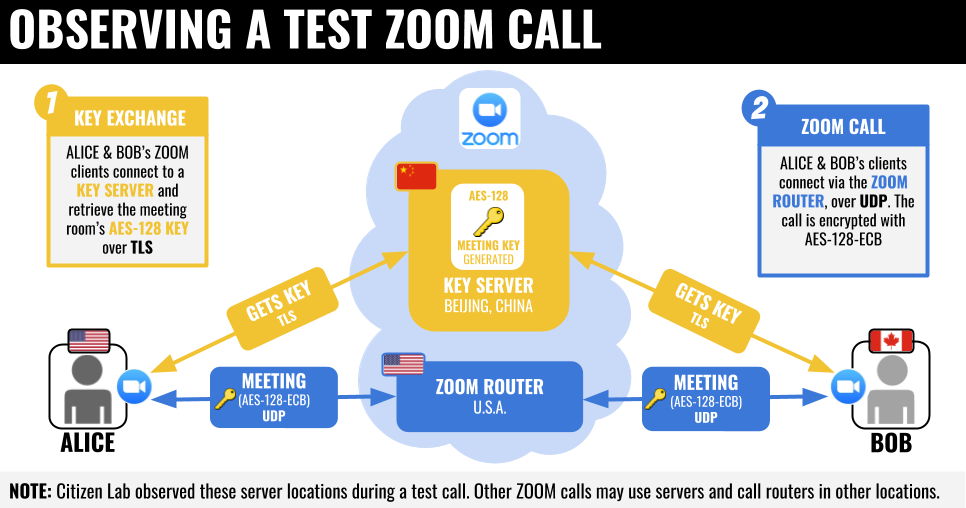
The University of Toronto's Citizen Lab examined transmissions through Zoom and found that a single encryption key (AES-128) was used to encrypt and decrypt audio and video for all participants in each meeting. These AES-128 keys can be easily intercepted along the way. They're also sent using a mode called electronic codebook (ECB), which preserves patterns within the encryption rather than fully coding or disguising them. As security guru Bruce Schneier puts it, "Using ECB mode indicates that there is no one at the company who knows anything about cryptography."
What's more, the encryption keys are often sent to servers in China, even if no one on the call is located there. Test calls between the U.S. and Canada showed keys routed to Beijing during the process. Perhaps that isn't surprising, considering that Zoom owns two companies in China where its software is developed (although the company has its headquarters in Silicon Valley). However, the Chinese government has the authority to inspect all data transmitted into China and this is a third-party risk that your organization must be willing to accept.
It's worth noting that Zoom may be pressured or obligated to share its encryption keys with authorities in China.
In April of 2020, the Windows Zoom client was revealed to have a known vulnerability that allows password credential theft. While Windows 10 Enterprise has Virtualization Based Security features to block these attacks, consumers and Windows 10 Pro users are out of luck until this vulnerability is patched. (Group Policy can also be configured to mitigate the vulnerability, but this doesn't really help consumers.)
Privacy Concerns and Consumer Protection Failures
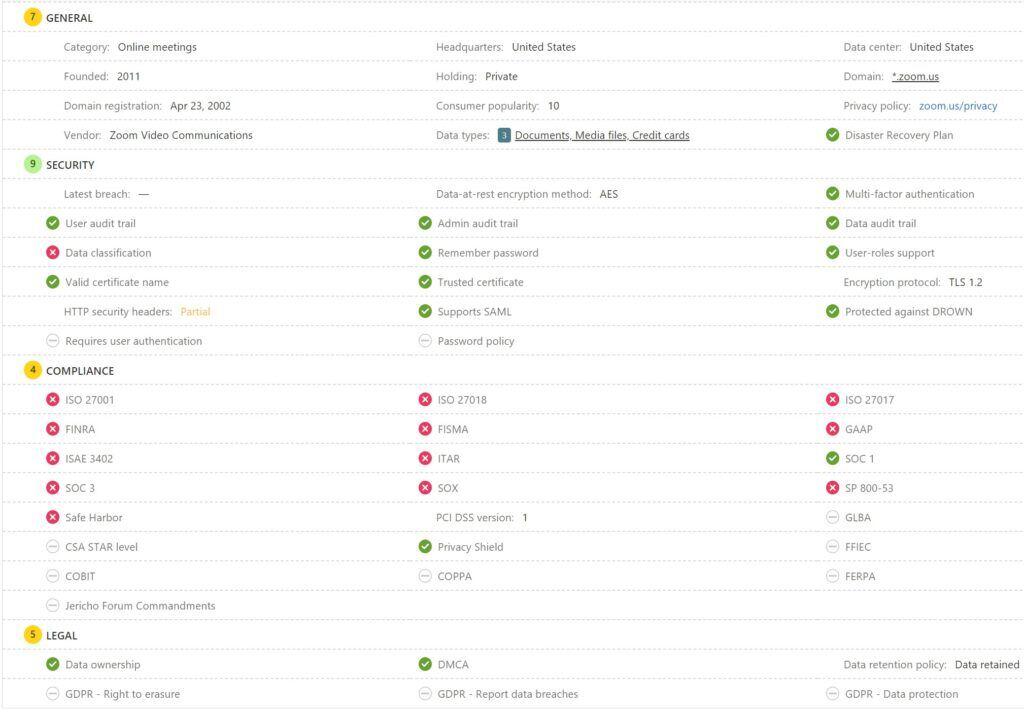
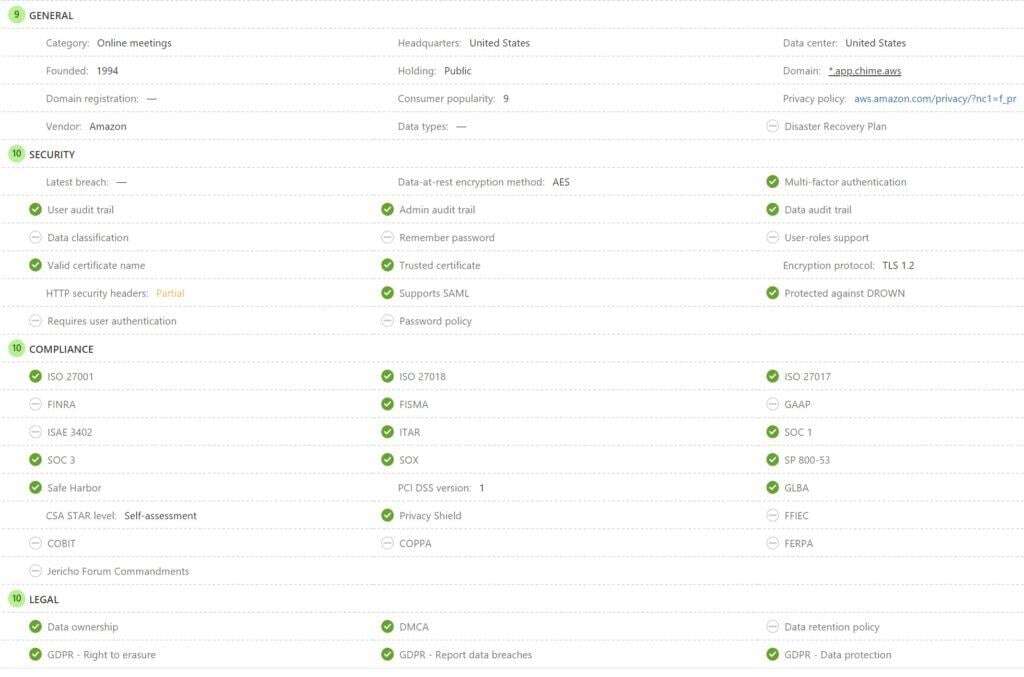
Microsoft Cloud App Security (MCAS) is a Shadow IT discovery tool that ranks over 20,000 companies across more than 70 risk factors. Zoom averages a 6/10 rating in MCAS and in the screenshot below, you can see its failure to adhere to common compliance frameworks and consumer privacy laws. If you work in education, Zoom is not FERPA (Family Educational Rights and Privacy Act) compliant, which should prompt you to leave the platform as soon as possible.
The folks at Zoom like to use this idea of "commonly accepted definitions" as a way to cover up both security and privacy concerns. Up until the end of March, their privacy policy stated, "In our humble opinion, we don't think most of our users would see us as selling their information, as that practice is commonly understood." Zoom does collect a long list of personal data from its users, which it shares with many third-party trackers. It gives out surveillance data for profit, and it makes it easy for users to proceed without seeing or accepting this.
Other digital platforms collect data in a similar way, but Zoom's access has extended even to the content shared while using the service. This has resulted in recent lawsuits for violation of the California Consumer Protection Act, and an investigation by the New York State Attorney General.
When you sign up for a free online consumer product or service, you are likely the product. And all of your data is probably being sold to third-parties.
Shaky Foundations and Knee-jerk Reactions
Zoom has become a lot more popular in recent weeks, but it's got a history of sketchiness that goes back further. Last summer Apple issued its own update to remove Zoom software from Macs after it discovered that Zoom used a hidden web server on Macs, ostensibly to provide additional convenience. This web server created a serious vulnerability that allowed any website to start a Zoom call automatically on a user's computer with the webcam on, without the user's direction.
This January, Check Point Research published a report that pointed out flaws which allowed uninvited hackers to listen in on large Zoom meetings. And last month the app was found to be leaking user data such as email addresses and photos because of a flaw in the way contacts are organized.
In a blog post from April 4th, Zoom said it will be enabling meeting passwords by default on its free tier to prevent Zoom bombings. This means if you're paying for Zoom, you will still be vulnerable. And there has been no announcement yet on plans to implement industry standards for end-to-end AES 256-bit encryption without ECB mode.
Better Collaboration Options than Zoom

At the end of 2019, Zoom had fewer than 2,000 employees worldwide, including sales and administrative staff. By comparison, Microsoft has over 3,500 employees working in their cyber security division alone. In addition, Zoom uses labor arbitrage by hiring developers in China at lower wages, and then selling the product at US rates.
This is a stark contrast to your tech behemoths. With Azure / GCP/ AWS, you know where your data is stored, how it's handled, and that they're adhering to data sovereignty rules. (And paying hefty fines when they run afoul.) Zoom simply does not have the resources required to keep up with the security demands required by their recent explosive growth.
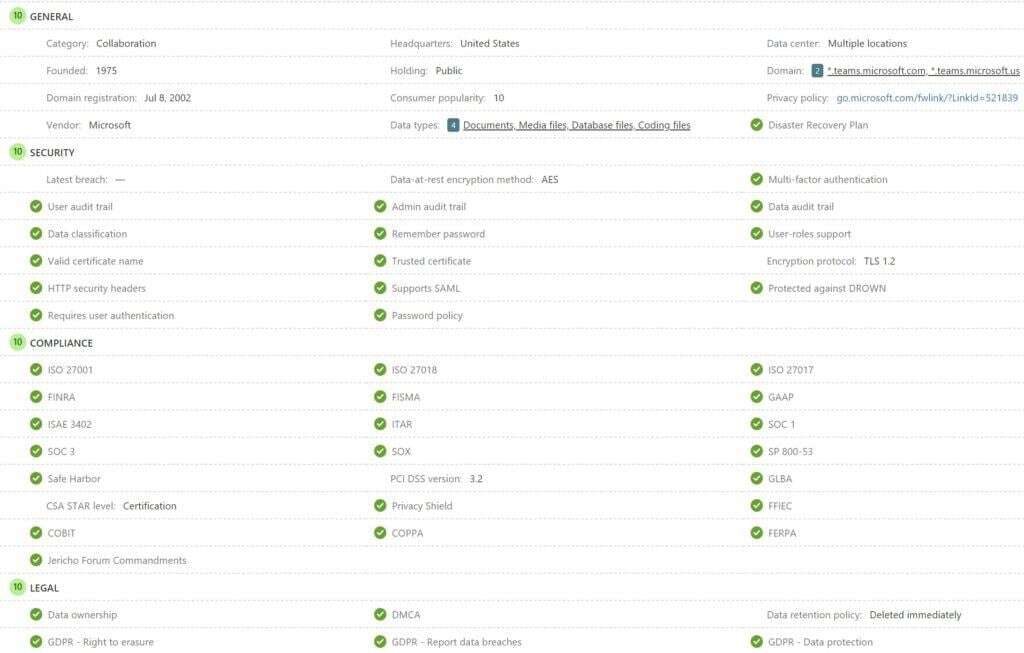
For more secure video calls, it's a better idea to go with an app from a well-known company with a good security reputation. Microsoft has the most secure and compliant offerings, with Amazon and Google close behind. (Lagging mostly because Alexa and Google Assistant are recording everything you say with loosely defined data retention policies.)
- Skype has been around for a good while and was acquired by Microsoft in 2011. It's had its ups and downs in popularity since then, but it's been significantly overhauled in the last couple years and is ready for a comeback.
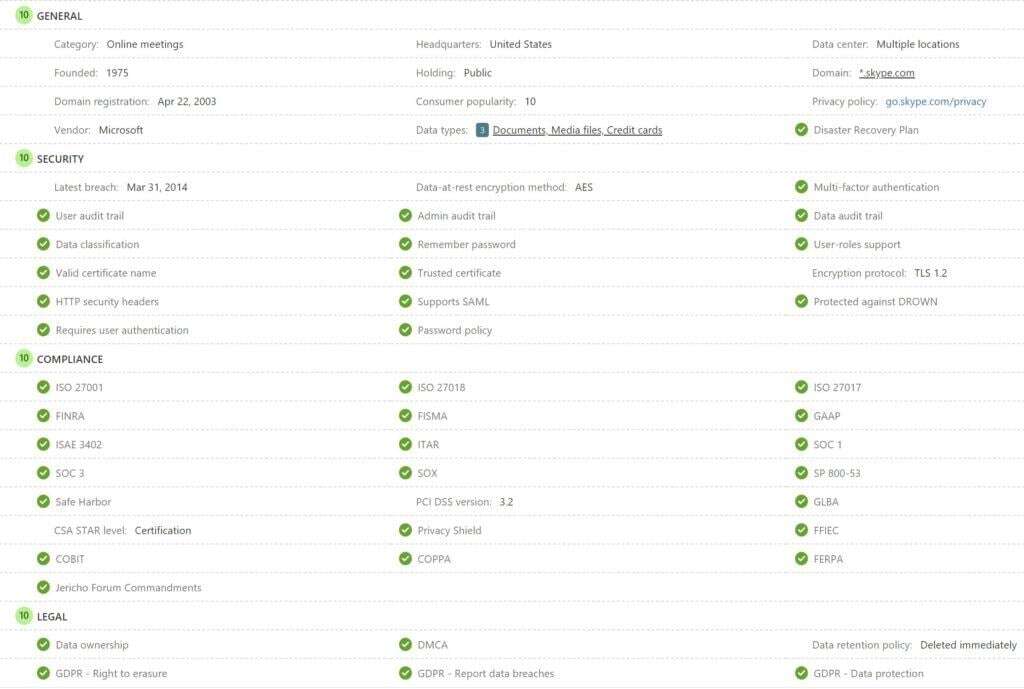
- Microsoft Teams evolved out of Skype for Business in 2017 and is now part of Office 365. It's a well-built platform designed especially for work environments. It's free for educators and non-profits, and Microsoft is also offering a free six-month trial for other businesses in response to the COVID-19 quarantine. There is also an entry-level always-free tier of Microsoft Teams. For educators, it's also important to note the Microsoft Teams and Skype are both FERPA compliant. These tools alone keep Microsoft at the top of Gartner's Magic Quadrant. And as of December 2021, Teams Essentials is an option that makes it even harder to justify using Zoom.
- Amazon Chime is a lesser known but secure video chat platform. While it hasn't been certified for as many compliance frameworks as Microsoft, it meets the needs of many of the major frameworks and privacy laws.
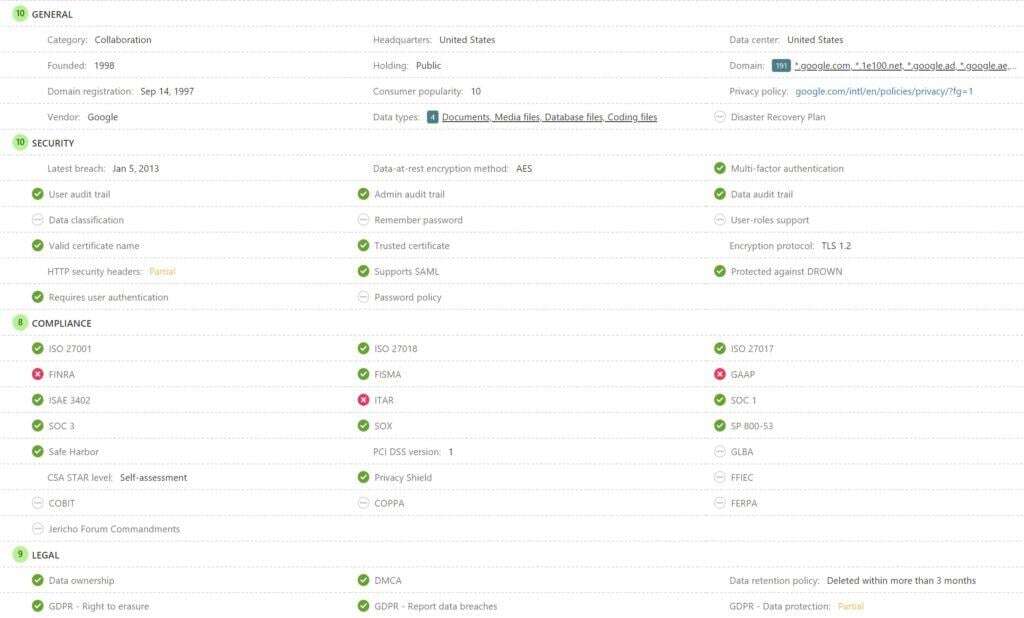
- Google Meet
Hangoutsemerged out of Google+ Messenger and Google Talk in 2013. This may be a convenient option especially for organizations already on G Suite / Google Apps as you're already familiar with the Google ecosystem.
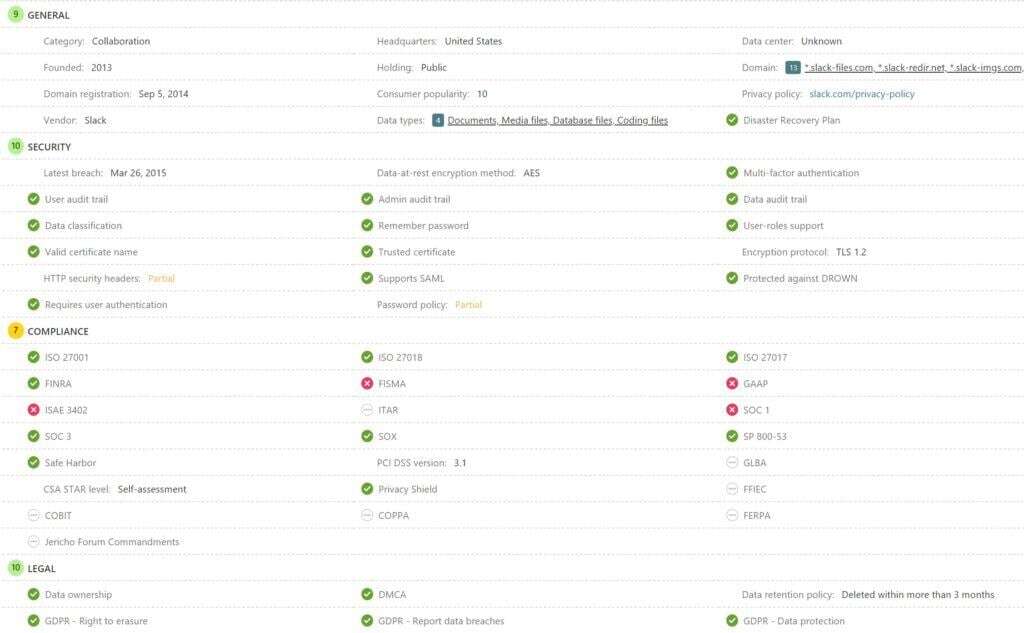
- Slack has been around since 2013 and as of 2019, has fewer than 2,000 employees. The significant difference between Slack and Zoom, is that Slack is a business-oriented platform. Businesses run on trust and Slack uses trusted industry standard encryption technology. By focusing on business users, Slack's development team has built security into their platform. Zoom will be struggling to bolt-on security to their platform over the coming months. And there's a strong chance that they still won't get it right.
- Webex by Cisco is a well-known and trusted solution. If you don't standardize on Microsoft 365, Cisco has the next best holistic Zero Trust security offering.
[caption id="attachment_2508" align="aligncenter" width="2211"]
 Webex is owned by Cisco and has been a trusted business communication platform for years.[/caption]
Webex is owned by Cisco and has been a trusted business communication platform for years.[/caption]
Compliance Results for Other VoIP & Video Services
There are plenty of other vendors in the VoIP and Video space. The following gallery contains some of the more common but less compliant services.
- 8x8
- Discord
- Facebook Messenger
- GoToMeeting
- RingCentral
- Twitch





How do I Protect a Zoom Meeting?
If you do find yourself on Zoom for whatever reason, take precautions:
- Use a password instead of the Waiting Room feature.
- Keep your meeting IDs private.
- Be aware of your host's capabilities.
- Treat the meeting and any data being shared as if the entire world is watching.
- Offer to host the meeting yourself on another platform.
The company is attempting to respond to the uproar about all of these vulnerabilities. But your safest bet is to explore one of the alternatives above. Because of Zoom's security and privacy issues, SpaceX and NASA are now prohibiting use of the app among their employees. If you're doing business or sharing private information, you need to adopt that policy too. Otherwise you will fail your next compliance audit.
Infused Innovations is protecting our clients by marking Zoom as an unsanctioned app in Microsoft Cloud App Security, and enforcing this policy on endpoints via Microsoft Defender ATP. If you're already on the Microsoft Threat Protection stack, this process takes about 2 minutes to complete. If you haven't made the jump yet, we offer free cybersecurity roadmap sessions and Zero Trust Security Accelerators to get your organization protected quickly.
*Update 7/28/2020:
Below is an updated compliance review for Zoom:

Stay connected. Join the Infused Innovations email list!
Share this
You May Also Like
These Related Posts

Microsoft Teams for Education
New Microsoft Teams Essentials Competes with Zoom

No Comments Yet
Let us know what you think