Just as a soldier stands guard, ready to defend against surprise attacks, so stands this duo of SIEM + SOAR for your Security Operations Center (SOC). And like a hawk with an overhead view, it does so from the cloud. Throw in a bit of AI, and you have Azure Sentinel. It provides intelligent security that collects data, detects and investigates threats, and responds rapidly.
Azure Sentinel is now generally available!
Microsoft recently announced that after feedback from over 12,000 trials, they've made Azure Sentinel generally available. This is exciting news for those looking for the combined data processing capabilities of a SIEM and the quick artificial intelligence of a SOAR. Here's a little more detail about some of Azure Sentinal's new capabilities that just went online.
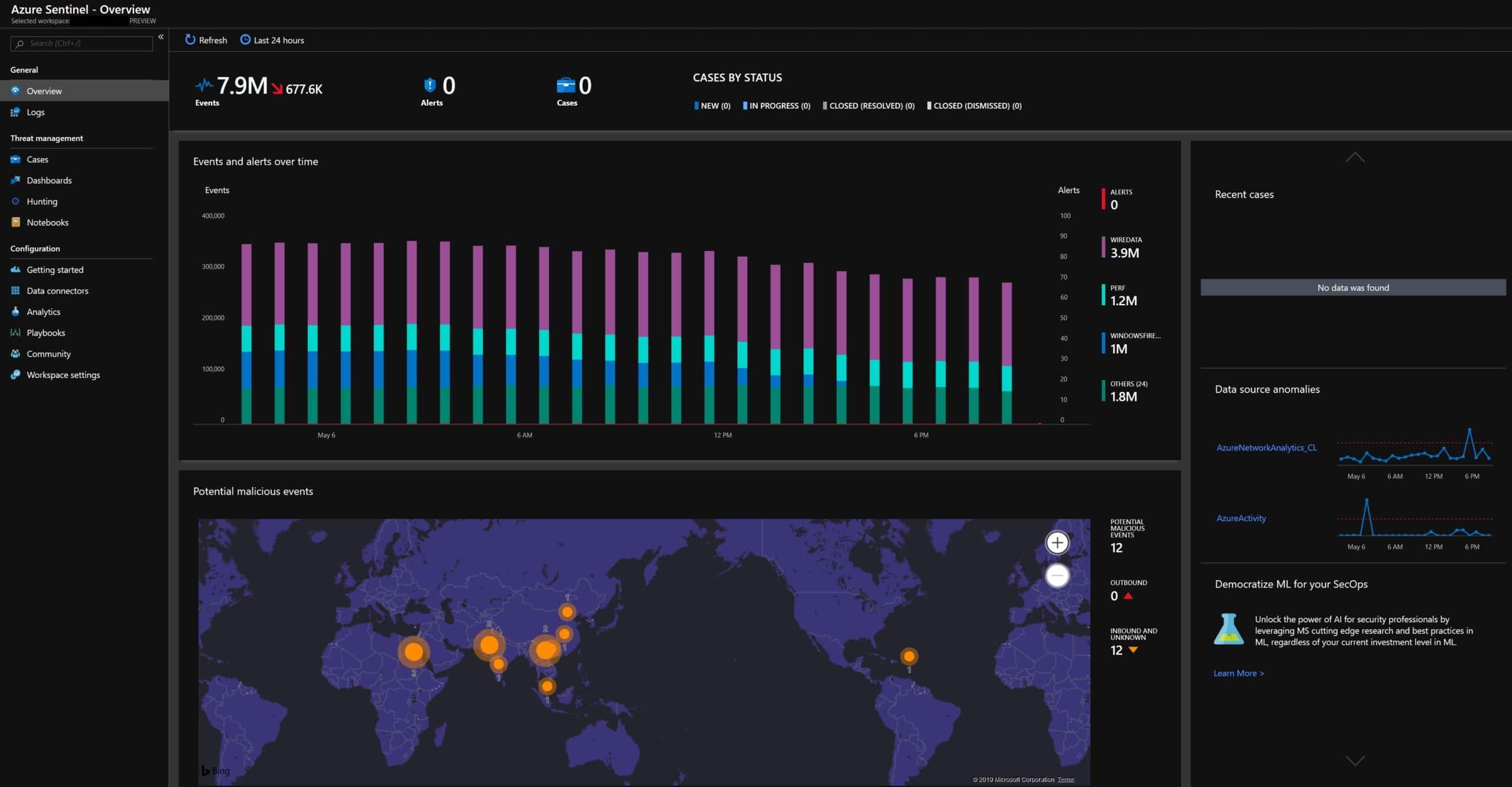
Virtually unlimited data collection and analysis
Lots of data sources are built-in or easily enabled in Azure Sentinel. Microsoft also offers new connectors for services such as Cloud App Security, as well as a growing number of third-party connectors, to seamlessly ingest and analyze data. If you're a visual person (who isn't?), workbooks allow you to easily view and analyze your data. You can use and modify existing workbooks, or you can create your own.

Analytics and Machine Learning for threat detection
Likewise, there are over 100 built-in alert rules, or you can create your own with a new alert wizard. Microsoft is also previewing a couple of different Machine Learning options. One uses proven Machine Learning models to identify threats and anomalies accurately. The second uses a technique called fusion which connects data from multiple sources to detect 35 different threats from various points on the kill chain.
Faster hunting, investigation, and response
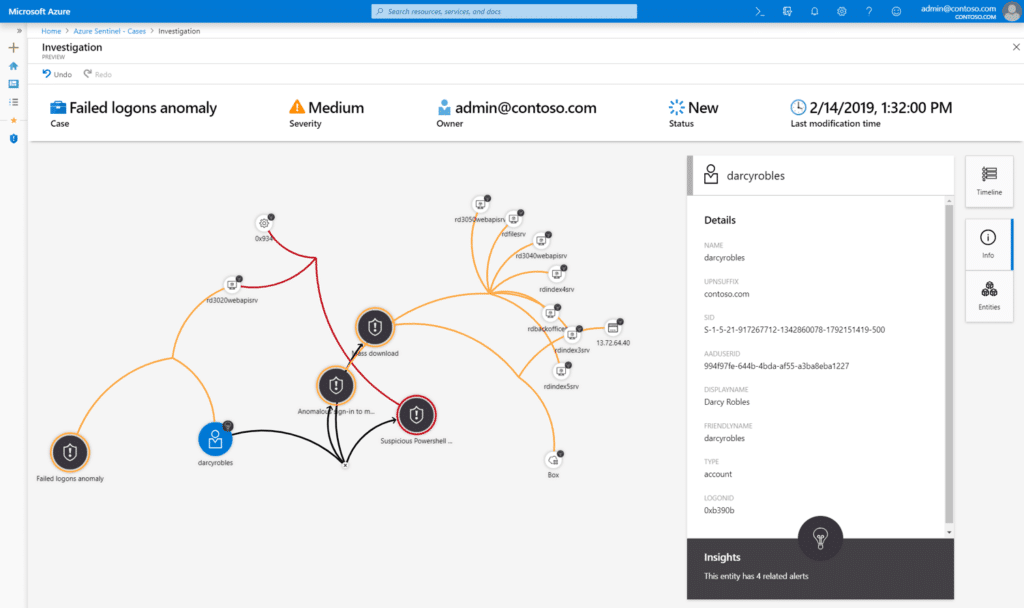
Hunting is traditionally rather time-consuming. But luckily we're no longer in the hunter-gatherer era: today's Sentinel combines a great (and growing) collection of hunting and exploratory queries with python libraries to get the task done very quickly. You can use these in Jupyter Notebooks and bookmark them accordingly. Alerts that require further investigation become incidents. You can decide which alerts trigger the creation of these incidents with the help of tagging, comments and assignments. Sentinel offers new actions and playbooks to streamline incident automation with Azure Logic App. And once again, you have visuals like the new investigation graph preview to give you a clearer picture of what you're dealing with.
Free Azure Sentinel Proof of Concept
Check out Forrester's Total Economic Impact Study on Azure Sentinel, which showed a 201% return on investment within three years. Azure Sentinel provides strong security and saves money. We know you want to jump on this. So we'll make it easy for you and free.
Our pricing guide for Azure Sentinel is also available to help clarify Microsoft's pricing. If you're interested in getting your hands dirty, you can follow our deployment guide for Azure Sentinel.
To read about a different security approach that doesn't rely on detection, see our article on Content Disarm & Reconstruction (CDR).
Stay connected. Join the Infused Innovations email list!
Share this
You May Also Like
These Related Posts
Step-by-Step Guide to Deploy Microsoft Sentinel
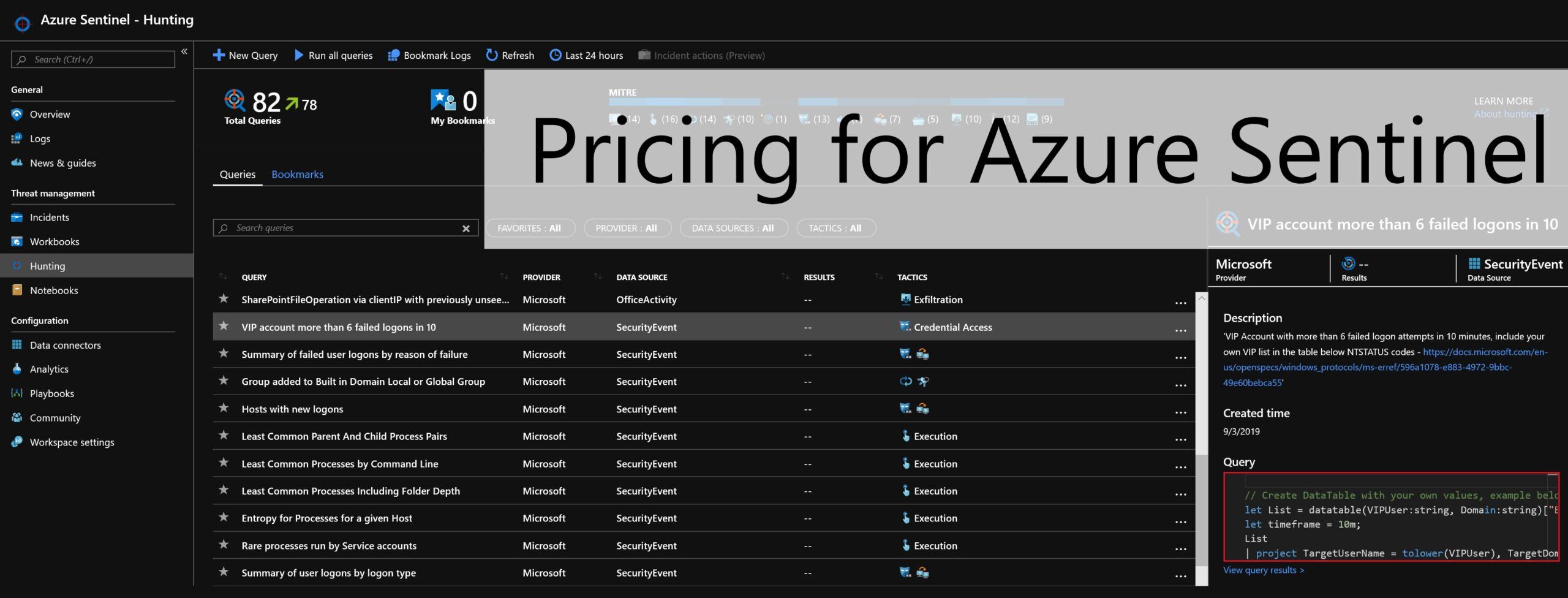
Pricing for Azure Sentinel is GA
No Comments Yet
Let us know what you think